Group Policy gives users administrative control over people and computers in the user’s network. By using Group Policy, users can define the state of someone’s work environment once, then rely on Windows Server 2003 to continually force the Group Policy settings applied across an entire organization or to specific groups of people and computers.
Group Policy Advantages
- Users can assign group policy in domains, sites, and organizational units.
- Group policy settings reflect all persons and computers in domain, site, and organizational unit.
- No one in network has rights to change Group policy settings. By default, only the administrator has full privilege to change, so it is very secure.
- Policy settings can be removed and the changes can be further rewritten.
Where GPOs Store Group Policy Information
Group Policy objects store their Group Policy information in two locations: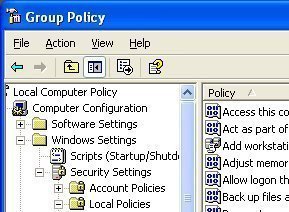
- Group Policy Container: The GPC is an Active Directory object that contains GPO status, version information, WMI filter information, and a list of components that have settings in the GPO. Computers can access the GPC to locate Group Policy templates. When the domain controller does not have the most recent GPO version, replication occurs to obtain it.
- Group Policy Template: The GPT is a folder hierarchy in the shared SYSVOL folder on a domain controller. When a GPO is created, Windows Server 2003 creates the corresponding GPT that contains all Group Policy settings and information, including administrative templates, security, software installation, scripts, and folder redirection settings. Computers connect to the SYSVOL folder to obtain the settings.
The name of the GPT folder is the Globally Unique Identifier (GUID) of the GPO created. It is identical to the GUID that Active Directory uses to identify the GPO in the GPC. The path to the GPT on a domain controller is systemrootSYSVOLsysvol.
Managing GPOs
To avoid conflicts in replication, consider selecting domain controller, especially because the GPO data resides in the SYSVOL folder and the Active Directory. Active Directory uses two independent replication techniques to replicate GPO data among all domain controllers in the domain. Two administrator’s changes overwriting those that another administrator made depends on replication latency. By default, the Group Policy Management console uses the PDC Emulator so that all administrators can work on the same domain controller.
WMI Filter
WMI filters get the current scope of GPOs based the user or computer’s attributes. In this way, the GPO’s filtering capabilities can be increased beyond the security group filtering mechanisms that were previously available.
A WMI filter can be linked to a GPO. When a GPO is applied to the destination computer, Active Directory evaluates the filter on the destination computer. A WMI filter has few queries that active Directory evaluates in place of the destination computer’s WMI repository. If the set of queries is false, Active Directory does not apply the GPO. If set of queries is true, Active Directory applies the GPO. The query is written with the WMI Query Language (WQL). This language is similar to querying SQL for WMI repository.
Planning a Group Policy Strategy for the Enterprise
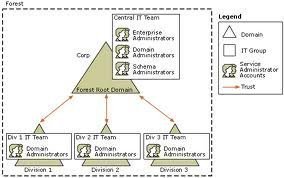
When planning an Active Directory structure, create a plan for GPO inheritance, administration, and deployment that provides the most efficient Group Policy management for the organization.
Also, consider how Group Policy will be implemented for the organization. Be sure to consider the delegation of authority, separation of administrative duties, central versus decentralized administration, and design flexibility so that the plan will be easy to use.
Planning GPOs
Create GPOs in a way that provides for the simplest and most manageable design, one in which users can use inheritance and multiple links.
Guidelines for Planning GPOs
- Apply GPO settings at the highest level: This way, users take advantage of Group Policy inheritance. Determine what common GPO settings for the largest container are starting with the domain then link the GPO to that container.
- Reduce the number of GPOs: Reduce the number by using multiple links instead of creating multiple identical GPOs. Try to link a GPO to the broadest container possible level to avoid creating multiple links of the same GPO at a deeper level.
- Create specialized GPOs: Use these GPOs to apply unique settings when necessary. GPOs at a higher level will not apply the settings in these specialized GPOs.
- Disable computer or use configuration settings: When creating a GPO to contain settings for only one of the two levels (user and computer), disable the logon, which prevents accidental GPO settings from being applied to the other area.


Naresh Durgam
what about the disadvantages of group policy?