A relational database stores data in separate tables instead of placing all data in one large table.
It then allows Data Base Administrators (DBAs) to define relationships between these tables.
These relationships enable DBAs to combine data from several tables for querying and reporting.
This is accomplished through the use of keys, which are database fields used to uniquely identify specific records in a table.
Relational database technology allows databases to be larger, faster, and more efficient.
Dr. Edger F. (Ted) Codd first developed the concept of a relational database in A Relational Model of Data for Large Shared Data Banks in 1970.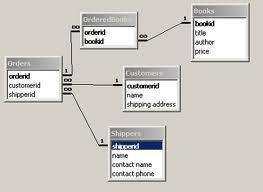
Dr. Codd defined thirteen standards that must be met before a database can be considered a relational database:
0. A relational DBMS must be able to manage databases entirely through its relational capabilities.
1. Information rule- All information in a relational database (including table and column names) is represented explicitly as values in tables.
2. Guaranteed access- Every value in a relational database is guaranteed to be accessible by using a combination of the table name, primary key value, and column name.
3. Systematic null value support- The DBMS provides systematic support for the treatment of null values (unknown or inapplicable data), distinct from default values and independent of any domain.
4. Active online relational catalog-The description of the database and its contents are represented at the logical level as tables and can therefore be queried using the database language.
5. Comprehensive data sublanguage-At least one supported language must have a well defined syntax and be comprehensive. It must support data definition, manipulation, integrity rules, authorization, and transactions.
6. View updating rule-All views that are theoretically updatable can be updated through the system.
7. Set-level insertion, update, and deletion- The DBMS supports not only set-level retrievals but also set-level inserts, updates, and deletes.
8. Physical data independence-Application programs and ad hoc programs are logically unaffected when physical access methods or storage structures are altered.
9. Logical data independence-Application programs and ad hoc programs are logically unaffected, to the extent possible, when changes are made to the table structures.
10. Integrity independence-The database language must be capable of defining integrity rules. They must be stored in the online catalog and they cannot be bypassed.
11. Distribution independence-Application programs and ad hoc requests are logically unaffected when data is first distributed or when it is redistributed.
12. Nonsubversion-It must not be possible to bypass the integrity rules defined through the database language by using lower level languages.
Alternatives to the relational database model include the hierarchical model, network model, and object model.



Tasneem
Thankz for providing this answr in such an easy language which is vey convinient to understand…!:)
vinod
Thanks……