How to Remove a Keylogger
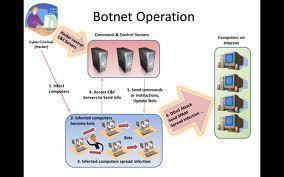
In the last few decades, computer science has changed the world. People now use computers to pay their bills, talk to their friends, and virtually everything else. Because of this dependence on computers, the vast majority of computer users have opened a portal into their homes that hackers and cyber thieves can use to steal …