Sometimes instead of encrypting a file or a set of files, you want to encrypt an entire file system, partition, or disk.
One of the chief advantages of this approach is that, once you have entered your encryption key, the encryption becomes transparent to both you and your applications. When you power off your computer, your data is securely encrypted. It is the best of both worlds.
What is Whole Disk Encryption
Whole disk encryption is a process in which every bit of data that is on a disk is encrypted using software or a hardware based method. Typically, whole disk encryption means that most everything on the disk is encrypted including the software that does the encryption, but the master boot record (MBR) must be left unencrypted. This means that part of the disk is unsecured.
However, some types of hardware-based whole disk encryption that make it possible for the entire boot disk, including the MBR, to be encrypted. This guarantees maximum security.
Benefits of whole disk encryption:
- Nearly everything gets encrypted. This includes the swap space and temporary files that can reveal very important data that one might not want revealed. People don’t think to manually encrypt these files.
- There is no need to manually encrypt files. The individual does not have to show discretion as to which files should be encrypted. Everything gets encrypted.
- Data destruction is immediate. Destroying the key makes the data that is contained completely useless.
- There is support for the pre-boot authentication which serves as an extension of the BIOS.
Disk Encryption Software and Documentation
Numerous solutions exist to enable you to do this, under Windows, Unix, and MacOS.
Disk Encryption under Unix
Under Unix one of the best options is loop-AES, which utilizes the AES algorithm to encrypt a loop file system.
Another option for Unix is Cryptoloop.
Allan Latham’s PPDD (Practical Privacy Disc Driver) is a Linux device driver which creates a device which looks like a disk partition. PPDD utilizes Bruce Schneier’s Blowfish algorithm.
Julian Assange’s Rubberhose is a unique Linux tool which combines encryption and steganography. Rubberose supports DES, 3DES, IDEA, RC5, RC6, Blowfish, Twofish and CAST.
Disk Encryption under Microsoft Windows
TrueCrypt is a free open-source disk encryption package for Microsoft Windows. TrueCrypt supports AES-256, Blowfish, CAST5, Serpent, Triple DES, and Twofish.
CompuSec is a free solution for Windows which implements a Fast AES algorithm.
Cypherix Cryptainer LE is a free solution for Windows which implements the Blowfish algorithm, but is limited to creating 25MB partitions.
CrossCrypt is an open source disk encryption package for Microsoft Windows which supports AES and TwoFish. Cross Crypt is designed to be compatible with aes-loop, which can be very useful for users who dual-boot Linux and Microsoft Windows.
FreeOTFE is open-source disk encryption software which supports AES and Twofish. For Linux dual-booters, FreeOTFE is designed to be compatible with Cryptoloop, dm-crypt, and LUKS.
BestCrypt is a commercial option which supports both Linux and Windows and is capable of utilizing the AES, GOST, Blowfish, or Twofish algorithms.
Another commercial option is PGPdisk, which supports both Windows and MacOS.
DriveCrypt is a commercial options with utilizes the AES algorithm and supports both Windows and Pocket PC’s.
Additional commercial packages for Windows include Paragon Encrypted Disk, and CryptoExpert.
Disk Encryption under MacOS
PGPdisk, is a commercial software package which provides disk encryption for both Windows and MacOS.
An older revision, PGPdisk 6.02i, is available at no cost. It has not been updated and it is not supported.
Types of Hard Drive Encryption
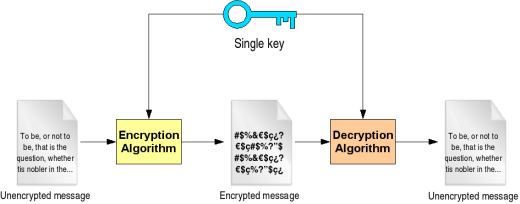
Password Encryption
Password encryption is, by far, the most popular form of hard drive encryption and usually consists of both a username and password. Password encryption techniques generally display a dialog window after the computer is booted and before the user is able to access the operating system. While password encryption is similar to normal log in procedures, it differs by implementing advanced encryption methods on the hard drive itself rather than simply preventing users from accessing the hard drive’s contents.
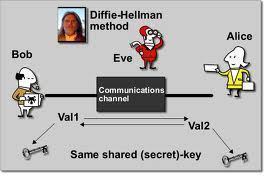
Smartcard Encryption
Smartcard encryption is similar to password encryption, but consists of a smartcard that is preloaded with the decryption key. Smartcard encryption can be used on any portable hard drive or flash memory device such as an SD card, USB drive, external hard drive, or actual smartcard. When the user connects the smartcard to the computer, he/she may also be prompted for a username and/or password for additional security.
Biometric Encryption
Biometric encryption is also similar to password encryption and represents one of the most secure forms of hard drive encryption. It uses the same techniques as other types of hard drive encryption, but uses a user’s biometric information as a private key for decrypting information. Biometric encryption can depend on vocal, optical, or signature recognition, in addition to a wide variety of other factors, although fingerprint recognition is much more common.

Mark Simmons
I’d like to point out the Truecrypt is available for Linux as well. There are two types of download: console/shell only or a nice GUI. See http://www.truecrypt.org/downloa