PGP (Pretty Good Privacy) is a data encryption and decryption program used in e-mail messaging, encrypting/decrypting texts, files, or even disk partitions, in order to provide security of data. The program was created in 1991, by Phil Zimmerman.
Pretty Good Privacy encryption is based on using a serial combination of data compression, hashing, public-key cryptography and symmetric-key cryptography. Public keys are bound to e-mail addresses or usernames.
 How Does PGP Work?
How Does PGP Work?
PGP is used for sending messages confidentially. It combines public-key and symmetric-key encryption. A symmetric encryption algorithm is used for message encryption. One symmetric key can be used only once. That is why it is called “a session key”. It is encrypted with the public key of the receiver and it can only be decrypted by the receiver. The receiver gets the encrypted message along with the session key.
Newer systems can create encrypted messages that can’t be decrypted by older PGP systems, even if there is a valid private key. That is why it is very important that parties agree on PGP settings before they start PGP communication.
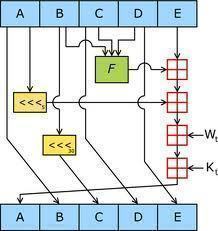
PGP supports integrity checking and message authentication. Integrity checking is used for determining whether there have been any alterations to the sent message. Message authentication is used to determine whether the message was sent by the entity or person claiming to be the message sender.
The person or entity sending the message will use either the DSA or RSA signature algorithms to make a digital signature. To do this, PGP will compute a hash from the plaintext, after which the digital signature will be created using the private key of the sender.
When it comes to security quality, PGP is very well spoken of. There is no method of breaking the encryption by computational or cryptographic means. Cryptographer Bruce Schneier described the early version of PGP as very close to military-grade encryption. However, early versions had certain theoretical disadvantages. It is always recommended to use current versions.
PGP encryption is used in data protection in long-term storage of information (e.g. disk files). Such storage options are also called “data stored”, “data at rest” or “not in transit”.
PGP encryption’s cryptographic security relies on the assumption that it is not possible to break the algorithms by using direct cryptanalysis. The RSA algorithm used in the original version of PGP was used for session key encryption. Its security relied on the nature of the one-way function of integer factoring. The second version of PGP used the symmetric key algorithm, but it has been found to have certain cryptanalytic flaws. Current version of PGP is considered secure are reliable, and even if there are insecurities – they are unknown to the public.
Current versions of Pretty Good Privacy include additional encryption algorithms, and so the vulnerability of these versions actually depends on which algorithm is used. In 2007, British police were not able to break PGP and they had to use RIPA legislation to get the keys/passwords. In 2009, a British citizen was jailed for nine months because he refused to provide police with keys for PGP encrypted files.

Follow Us!