Access control is the execution of limitations and restrictions on whoever tries to occupy a certain protected property, thereby keeping people as safe as possible. As modern society moves further into the cyber age, these access control systems become almost completely computer controlled. This article will further explain what access control is, how it works, and will list the different types.
What is Access Control?
Access control is the term used to describe how a person, mechanical device, or computer system uses both physical barriers and alarms to keep an unauthorized person from entering a specific area. Without knowing it, nearly everyone sees some form of access control everyday. For example, a door lock is a type of access control because it prevents unauthorized persons from entering a room or building. There are many different ways in which individuals/entities can prevent someone/thing from accessing their premises/belongings. The following are examples of how access control systems keep unauthorized users from accessing a system or area:
Access Control for Computers
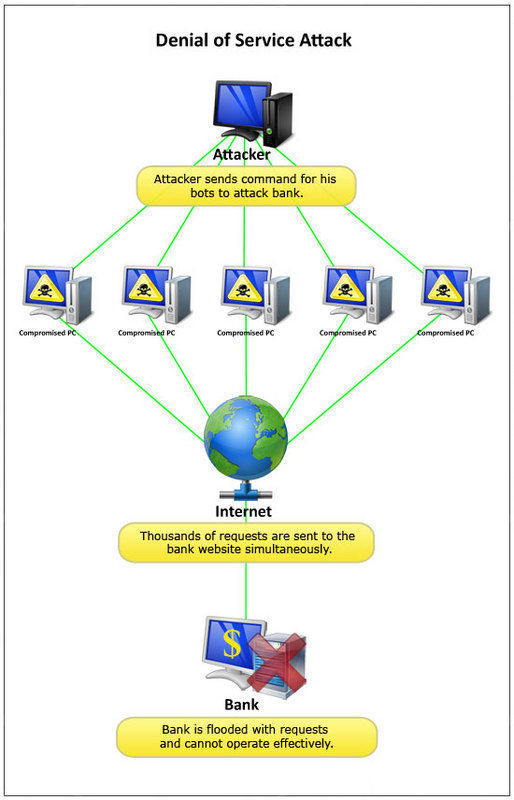
Nowadays, almost every computer user has a firewall or anti-virus, a pop-up blocker, and many other programs running on his/her computer. All of these programs are access control mechanisms that guard users from intruders. They inspect everything trying to enter the computer and either prevent or allow them to enter. Computers have complicated access control abilities. They ask for authentication and search for the digital signatures.

Physical Security
Physical security is usually the preferred method of access control. It involves a door, lock, wall, or some other object that physically prevents a person from entering a room or building. A door (with its handle) is the most common form of physical security. A door’s handle must be twisted in order to open or close the door. Without this handle the door would keep swinging and would not stop anyone from entering the room. The combination lock on a safe is another type of physical security. Generally, other access control sources such as identification scanners (which scan physical features, voices, and fingerprints), alarms, cameras, or armed personnel accompany physical security.
Non-Intelligent Readers
A non-intelligent access control reader (basic reader) is an access control system that simply reads the user’s input and has no control over whether or not access is granted. For example, an access control system that uses a number pad for PIN numbers or passwords is considered a non-intelligent access control reader. Likewise, an access control system that requires the user to swipe a card in order to access a room or account is also considered a non-intelligent access control reader. These types of readers are the most common and can be found on ATM machines and hotel doors.
Semi-Intelligent Readers
A semi-intelligent access control reader acts in the same manner as a non-intelligent access control reader but has some control over the actual physical security that prevents the user from accessing the room or object. For example, an access control system that uses a sensor to open a door, such as those often found in supermarkets, would be considered a semi-intelligent access control reader.
Intelligent Readers
An intelligent access control reader receives input from the user just as any other reader would, but has full control over whether access is granted or not. These types of systems can actually make decisions based on the situation and are fully independent from other computer systems. For example, an access control system that requires the user to provide a fingerprint and retinal scan would not be considered an intelligent access control reader by itself. However, if that system were able to notice that the user’s palms were sweaty and eyes were dilated and made a decision to not permit the user into the account or building, it would be considered an intelligent access control reader.
Huge Market for Access Control
The access control market is a rapidly growing one and may soon manifest itself in unimaginable ways. Nowadays, security access control is a necessary business component. There are many ways to create this security. Some companies hire a security guard to stand in the gateway. There are many security devices that prevent or permit access such as a turnstile. The best, most effective access control systems are computer operated.

Follow Us!