Two factor authentication is term used to describe any authentication mechanism where more than one thing is required to authentate a user.
The two components of two factor authentication are:
- Something you know
- Something you have
Traditional authentication schemes used username and password pairs to authenticate users. This provides minimal security, because many user passwords are very easy to guess.
In two factor authentication, the password still provides the something you know component.
In the most common implementations of two factor authentication, the something you have component is provided by a small token card. The token card is a compact electronic device which displays a number on a small screen. By entering this number into the system when you attempt to authenticate (login), you prove that that you are in possession of the card.
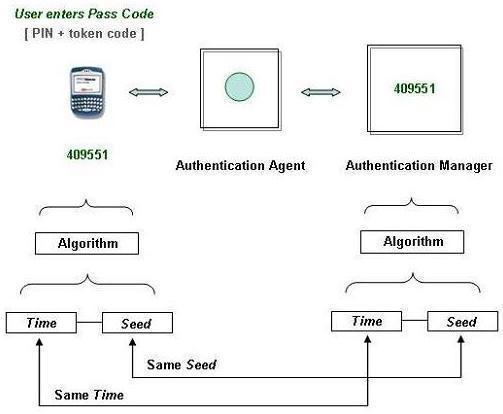
The number displayed by the card changes frequently, usually every 30 or 60 seconds. The system which you are authenticating to knows the number which should be on your screen. If the numbers match and your password is correct, you are authenticated.
To increase security, the electronic device is sometimes protected with a PIN. In these systems, you must enter the correct PIN before the correct numbers are displayed.
Two factor authentication can also be implemented using a physical key. That would allow only local access to wherever the lock was physically present. Due to this limitation, almost all two factor authentication systems utilize electronic tokens.
Two Factor Authentication and Biometrics
One of the competing technologies for implementing two-factor authentication is biometrics. Biometrics uses something you are as an authentication factor instead of the something you have mechanism utilized in traditional two-face authentication.


Follow Us!