Wireless traffic is considered to be those Internet protocol packets that are transmitted through an 802.11a, b, g, n, or i wireless protocol.
Monitoring Requirements
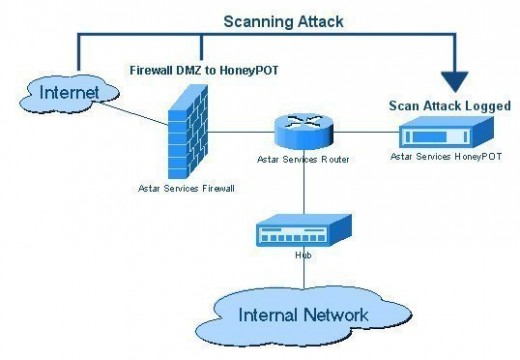
There are a few things to consider when planning to setup wireless traffic monitoring. First, the user must determine what kind of traffic will be monitored. Is the traffic to or from local systems or to and from a system the user has no direct control of? Second, the user needs to have the appropriate wireless adapter installed in his/her system, with its proper driver loaded. Thirdly, the user needs monitoring software on that system that can sniff packets on that interface.
Traffic Selection
If the user is attempting to monitor traffic to and from a specific system that he/she administrative access to, any sniffer capable of attaching to his/her local wireless interface is all that is necessary.
In order to monitor traffic between systems that the user has no administrative access to, he/she should ensure that the wireless adapter can go into monitor mode. Wireless adapters placed in monitor mode do not normally operate for other connectivity at the same time. So, when using a wireless adapter for Internet access, the user needs two wireless interfaces installed in order to maintain Internet connectivity while monitoring. In some cases, users need to place their system kernel in monitor mode prior to using wireshark. Check the adapter and operating system documentation to determine how to do this.
Wireless Adapters
Some wireless adapters are better suited to sniffing packets than others. Not all adapters can properly detect and report errors and others have drivers that are not very suited to packet sniffing. Cisco Aironet cards, Prism II cards, and Orinaco Silver and Gold cards are considered the best cards to perform monitoring from, but they are only a few of many that have the capability and the proper drivers available. Research which cards are available for the operating system to be used and procedures necessary for their driver install before purchasing any card.
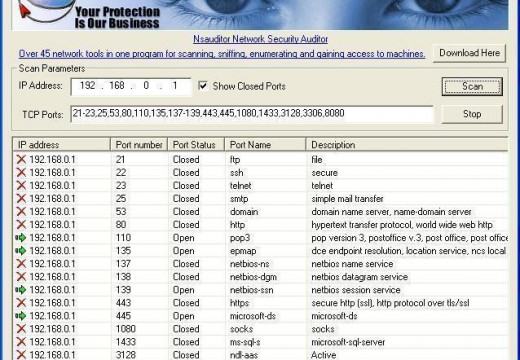
Wireless Sniffers
A free full-featured multi-platform sniffer that supports most wireless adapters is wireshark. This package is very suitable for debugging communications between systems and format output in a way that assists the user in identifying protocol components. It also provides additional information about those protocols that are not always available in other sniffers, making it quite simple to use with limited training. Users will still be required to understand the protocols they are debugging to get the full benefit of the sniffer output.
Airsnort is a wireless encryption key recovery program that allows users to determine what the lost or unknown encryption keys for their wireless devices are after passively monitoring packets for a period.
Another tool named Aircrack-ptw is similar to Airsnort. However, it has been more refined for WEP key determination and can decode them in much less time since it requires significantly fewer sniffed packets to do so.
Kismet is a wireless network detection tool that can also sniff packets and provide intrusion detection services if it is properly configured. Kismet is a very useful tool for conducting wireless network audits, as it has all the proper utilities required for performing audits.
Additional Equipment
It may be helpful for the user to ensure that he/she has better equipment to perform monitoring duties. Equipment that may be useful for wireless network audits include:
- a long range 802.11 network card
- a high-gain yagi directional antenna
- an omni-directional antenna
- pigtail cables for the yagi and omni-directional antennas
- a USB GPS (Global Positioning System) adapter
Legal Concerns
Users should keep in mind that monitoring or otherwise auditing networks and systems they do not own may be illegal in their country or state. Consult legal counsel if unsure of the legal ramifications when performing activities that involve someone else’s property.

Follow Us!