Network Infrastructure Security Overview
Network infrastructure refers to the grouping of physical hardware and logical components which are needed to provide a number of features for the network, such as connectivity, routing and switching capabilities, network security, and access control. The physical infrastructure of the network refers to the physical design of the network together with the hardware components. The logical infrastructure of the network consists of all the software components required to enable connectivity between devices, and to provide network security. The network's logical infrastructure consists of software products and networking protocols and services.
While Windows Server 2003 provides a number of features and tools when you install it on a computer, you have to implement additional features and functionality on a server to provide the services and capabilities required by the organization and its users.
There are a number of different risks that have an impact on an organization. Some of the primary threats which you should address are listed here:
-
Environmental threats pertain to both environmental disasters and disasters due to human intervention. Examples of environmental threats are fires, earthquakes, storms, faulty wiring, and so forth.

-
Accidental threats relate to threats which are caused without malicious intent. Accidental risks occur when an employee accidentally deletes important files, or modifies data that should not have been changed.
-
Deliberate threats relate to threats which are caused with malicious intent as the primary objective. Examples of deliberate threats are viruses, Trojan horses, and all other network attacks caused by hackers and intruders.
A typical security life cycle is consists of the following processes:
-
Determining and designing the security infrastructure: The design phase of the security life cycle includes elements such as identifying the resources of the organization that needs to be secured, and then designing the security infrastructure to protect these resources. The security design team should be accountable for creating and designing security policies for the organization.
-
Deploying and implementing security features and security policies: The security design team should also be responsible for implementing security features and security policies.
-
Continually managing the security solution: All security software should be upgraded as necessary, and audit logs should be regularly examined.
A number of common steps or processes have to be completed to design network infrastructure security:
-
Determine the security requirements of the organization.
-
Plan network security which should be implemented.
-
Establish and create secure boundaries.
-
Implement security technologies for the network.
-
Implement server security technologies.
-
Implement application security technologies.
-
Implement user security technologies.
-
Implement an auditing strategy.
-
Implement a network monitoring strategy.
A few methods of securing your network infrastructure are listed here:
-
Physically secure all mission-critical network servers: A few guidelines and recommendations for implementing physical security are detailed below:
-
All servers should be secured in a locked server room.
-
Only those individuals that need access should be permitted to access the server room using a key or security code. You can also implement a mechanism that monitors who enters and leaves the server room.
-
All hubs, routers and switches should be placed in a wiring closet, or in a locked cable room.
-
You should use case locks on your servers. You can also install case locks on other systems that can be physically accessed.
-
You should restrict access to the floppy drive as well.
Set a BIOS password on all systems. This would prevent an unauthorized person from accessing the BIOS. -
You should change the operating system selection timeout interval to 0 in order for Windows to boot automatically.
-
When you are setting up Windows, disconnect the server from the Internet.
-
Install Windows operating systems to a NTFS partition.
-
Ensure that you use a strong local administrator password during setup.
-
-
Using the NTFS file system and its security features.
-
Using the Encrypting File System (EFS).
-
Securing network access points.
-
Enforcing user authentication.
-
Securing network access.
-
Enforcing the use of strong passwords.
-
Securing confidential network service data as it moves over the network.
-
Securing confidential application data as it moves over the network.
-
Securing confidential user data as it moves over the network.
Each Windows server operating system provides different features, and different security configurations which can be enabled to enhance network security and server security. Before deciding on the operating system to utilize, you have to know which security features are required for your network design, as determined by the organization's requirements.
Most organizations use a security design committee or team to determine the security needs of the organization and to deploy security policies which can meet these requirements.
The members of the network security design committee should be knowledgeable on a number of factors, including the following:
-
The mission critical resources of the organization.
-
The security weaknesses or vulnerabilities of the organization.
-
The threats to which the mission critical resources of the organization is exposed.
-
The resources which are mainly at risk.
-
The loss to the organization should particular resources of the organization be compromised.
-
The level of security needed to secure the organization's resources.
-
The security features and security policies which can be used to secure the resources of the organization.
-
The security features and security policies which are ideal to secure particular resources.
-
The impact of implementing security features and security policies on employees, users and administrators.
-
The requirements for deploying identified security solutions.
Finding the Balance between Security and Usability
One of the trickiest challenges of designing network infrastructure security is to establish a balance between security and usability. The network has to be secure so that valuable network resources can be protected, but it also has to allow the sufficient extent of usability. Networks that are too secure, or that have an exceptional high level of security can end up having low levels of usability. This typically leads to users not being able to access network resources and services. On the other hand, a network that has an exceptionally low level of network security has a somewhat higher level of vulnerability to network attacks and data corruption.
To find a balance between security and usability, the following approach is recommended:
-
Determine the risk to which the network and its data is exposed to, and then establish the level of security needed to alleviate and protect against these risk: This would typically involve an assessment of the physical security of your network infrastructure:
-
Assessing whether the physical building is secured.
-
Assessing whether the network location is secured.
-
Determining whether access to the physical building is access controlled.
-
Determine the impact of data being compromised.
-
-
Determine which data is valuable and mission critical data: Valuable and mission critical data would typically include usernames and passwords, confidential customer information, company financial and legal information, and so forth. As mentioned previously, one of the challenges you face when designing network infrastructure security is to find a balance between security and usability. You also need to find a balance between securing valuable or mission critical data and performance of the network. For each traffic class that should be secured, an additional layer of processing is added to the actual processing of IP packets. This makes the process of identifying valuable and mission critical data a bit more complicated. You need to find an acceptable balance between applying too much security and applying too little security.
-
Determine which security policies need to be implemented. You should only attempt to determine the security policies that need to be implemented after you have determined the risk that the network and its data is exposed to, and the data that is considered valuable and mission critical data. The security policies that you identify should be based on all of this previously collected information. Windows Server 2003 and the IPSec framework specify three levels of security. IPSec is a framework of open standards which can be used to encrypt TCP/IP traffic. IPSec works by encrypting the information contained in IP datagrams through encapsulation. This in turn provides network level data integrity, data confidentiality, data origin authentication, and replay protection. To secure data moving over the intranet, extranet, and Internet, IPSec can be used. The three levels of security specified by Windows Server 2003 and the IPSec framework are listed here:
-
Minimum security level: This is the default level of security. The minimum security level has the following characteristics:
-
The system and its data is exposed to low risk, and not to substantial risk
-
IPSec is not implemented.
-
No confidential or valuable data is exchanged.
-
-
Standard security level: The standard security level has the following characteristics:
-
There are a number of computers and servers that store mission critical, sensitive data. These servers need to be secured.
-
Windows Server 2003 utilizes security policies to secure valuable data. The Client (Respond Only) and Server (Request Security) policies can be utilized to secure data.
-
-
High security level: The high security level has the following characteristics:
-
There a number of computers and servers that store highly sensitive data. These servers need to be highly secured.
-
All communication has to be secured.
-
The Windows Server 2003 Secure Server (Require Security) policy can be used to provide the highest level of security to secure data.
-
-
-
Identify how the optimal method of implementing security policies: There are a number of methods which can be used to implement security policies. The recommended method is through IPSec policies that comprise of a number of IPSec rules. An IPSec rule contains the following components:
-
A filter list.
-
A filter action.
-
An authentication method.
-
A connection type.
-
A tunnel configuration
When you configure and manage IPSec policies, you would basically be configuring a number of aspects of IPSec policies:
-
Assign the predefined default IPSec policies OR
-
Create customized IPSec policies that include customized IPSec rules and filters.
-
Control how IPSec policies are applied.
-
Apply IPSec policies at different levels on the network. IPSec policies can be applied at the following levels within a network:
-
Active Directory domain
-
Active Directory site
-
Active Directory organizational unit
-
Computers
-
Applications
-
-
-
Implement security technologies and management requirements. You have to ensure that these technologies are both implemented and available. ActiveDirectory was the important feature introduced in Windows 2000 because it brought about a few important domain structural changes. Domains in Active Directory use the DNS domain naming structure, and not the NetBIOS naming structure used in Windows NT domains. Because of DNS, Active Directory domains are structured in a hierarchical model. Domain trees is the concept used to describe hierarchically structured groups of domains with a contiguous namespace, while the grouping of trees with a noncontiguous namespaces are called forests. Active Directory should be deployed to ensure that the network infrastructure is as secured as can be. Active Directory enables you to perform policy based administration through Group Policy. Through group policies, you can deploy applications and configure scripts to execute at startup, shutdown, logon, or logoff. You can also implement password security, control certain desktop settings, and redirect folders. With Active Directory, permissions control access to resources, while user rights define what actions users can perform. Security groups are considered security principal accounts because they can contain user accounts. It is the security principal accounts that are used in authentication and access control. The security settings of a security principal account controls whether the user, group, or computers are authorized to access the following:
-
Active Directory
-
Domain controllers
-
Member servers
-
Client computers
-
Applications
-
Printer and file system objects
-
Other network components
-
-
You can apply standard permissions or special permissions to Active Directory objects. Access control and authentication are extremely important components in Active Directory security. Domain and forest functional levels provides the means by which you can enable additional domain-wide and forest-wide Active Directory features, remove outdated backward compatibility within your environment, and improve Active Directory security.
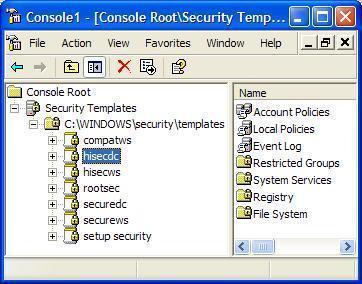
An organizational unit (OU) is a container that is used to organize Active Directory objects into logical administrative groups. An OU enables you to apply security policies, deploy applications, delegate administrative control for Active Directory objects, and to run scripts. A good security management strategy would be to group computers that have similar roles into Active Directory OUs. You can then apply IPSec policies and security templates to all the computers located within the OU. -
Implement a secure, yet simple method for users to access the necessary resources: As mentioned previously, you have to determine the balance between securing valuable data and allowing authorized users to access the necessary resources. The higher the level of security, the slower the response times users experience. Using group policies to control security policies, and using IPSec and smart cards are options that should be explored.
Determining Security Requirements of the Organization
To determine the security requirements of the organization, you have to include a number of business factors:
-
The business model that the organization uses greatly influences the type of security an organization implements. An organization that has world-wide branches would have different security requirements to a business that has a single office.
-
To successfully implement security, you have to know how business processes within the organization work. You have to ensure that security does not prevent business processes from being carried out.
-
As the business grows so too must the security policies and processes be able to cater for this growth.
-
Determine the risk tolerance of the organization. The level of risk tolerance would differ between organizations.
-
Determine whether there are any laws and regulations that the organization has to adhere to. This is especially important when you draw up the security design.
-
The management strategy being used should be included as well. Organizations can use either a centralized management strategy or a decentralized management strategy.
-
The existing security policies and procedures should be included when you define the security requirements of the organization
-
The financial stance of the organization would also influence which security design is implemented.
Assessing the existing security processes and security policies would typically involve determining what the current security processes and security policies are, and whether these can be improved to meet the security requirements of the organization.
There are a number of recommendations which you can use to match the business requirements to the security plan:
-
The organization uses business processes,
-
You should determine how these business processes flow and how the data associated with these processes flow.
-
You should determine the users that need to access services used in the business processes.
-
-
The organization uses a centralized management strategy,
-
You should minimize the number of domains
-
Include the management of administrative group membership.
-
-
The organization uses a decentralized management strategy,
-
You should determine the rights that users require.
-
You should determine whether users need administrative abilities on the network, and if yes, determine who those users are.
-
-
The risk tolerance level of the organization indicates an aversion to risks,
-
You should determine the risks that the organization is not prepared to tolerate.
-
Identify the actions which are necessary should the risk become a reality, and then include this in the security plan.
-
-
The organization expects business growth in the next number of years,
-
You should try to estimate how many users and computers will be needed to provide for future business expansion.
-
Try to determine how the business will be geographically dispersed.
-
Designing Security based on Technical Requirements
There are also a number of technical requirements which could have an impact on your security plan, that have to be met: The common technical requirements are listed here:
-
How users and computers are distributed has a direct impact on how security is implemented for an organization. The distribution and size of these resources would impact:
-
How Active Directory sites are defined.
-
How Active Directory domains and organizational units are defined.
-
-
Before network infrastructure security can be implemented, the organization has to determine what the desired levels of performance which have to be maintained are. For instance, deploying additional authentication methods, and implementing encryption technologies affect performance levels.
-
The methods in which data is accessed would affect the security plan. You should include all the components used to access data:
-
Users
-
Computers
-
Protocols
-
Services
-
Applications
-
-
How remote branches access the corporate network also has an impact on the security plan. Dedicated network links or virtual networking can be used to enable connectivity to the corporate network. Included in your security plan, should be the level of encryption that is required for WAN links.
IPSec Fundamentals Summary
IPSec is a framework of open standards for encrypting TCP/IP traffic within networking environments. IPSec works by encrypting the information contained in IP datagrams through encapsulation to provide data integrity, data confidentiality, data origin authentication, and replay protection. IPSec uses cryptography to provide authentication, data integrity, and data confidentiality services.
IPSec uses he Authentication Header (AH) protocol and Encapsulating Security Payload (ESP) protocol to provide data security on client computers, domain servers, corporate workgroups, LANs, WANs and remote offices. The Authentication Header (AH) protocol provides data authentication and integrity, and can be used on its own when data integrity and authentication are important to the organization but confidentiality is not. The AH protocol does not provide for encryption, and therefore cannot provide data confidentiality. The Encapsulating Security Payload (ESP) protocol ensures data confidentiality through encryption, data integrity, data authentication, and other features that support optional anti-replay services. To ensure data confidentiality, a number of encryption algorithms are used. The main difference between the AH protocol and the ESP protocol is that the ESP protocol provides all the security services provided by the AH protocol, together with data confidentiality through encryption.
When you install IPSec, the two main IPSec components which are installed are the IPSec Policy Agent and the IPSec driver. The IPSec Policy Agent is a service running on a Windows Server 2003 computer that accesses IPSec policy information. The IPSec Policy Agent accesses the IPSec policy information in the local Windows registry or in Active Directory, and then passes the information to the IPSec driver. The IPSec driver performs a number of operations to enable secure network communications such as initiating IKE communication, creating IPSec packets, encrypting data, and calculating hashes.
IPSec can operate in either Tunnel mode or in Transport mode. IPSec Tunnel mode should be used to provide security for WAN and VPN connections that use the Internet. In tunnel mode, IPSec encrypts the IP header and the IP payload. With tunneling, the data contained in a packet is encapsulated inside an additional packet. The new packet is then sent over the network. In Transport Mode, the default mode of operation used by IPSec, only the IP payload is encrypted. Transport mode is used for end-to-end communication security between two computers on the network.
The security features provided by IPSec are summarized here:
-
Authentication; a digital signature is used to verify the identity of the sender of the information. IPSec can use Kerberos, a preshared key, or digital certificates for authentication.
-
Data integrity; a hash algorithm is used to ensure that data is not tampered with. A checksum called a hash message authentication code (HMAC) is calculated for the data of the packet. When a packet is modified while in transit, the calculated HMAC changes. This change will be detected by the receiving computer.
-
Data privacy; encryption algorithms are utilized to ensure that data being transmitted is undecipherable.
-
Anti-replay; prevents an attacker from resending packets in an attempt to gain access to the private network.
-
Nonrepudiation; public key digital signatures are used to prove message origin.
-
Dynamic rekeying; keys can be created during data sending to protect segments of the communication with different keys.
-
Key generation; the Diffie-Hellman key agreement algorithm is used to enable two computers to exchange a shared encryption key.
-
IP Packet filtering; the packet filtering capability of IPSec can be used to filter and block specific types of traffic, based on either of the following elements or on a combination of them:
-
IP addresses
-
Protocols
-
Ports
-
To secure and protect data, IPSec uses cryptography to provide the following capabilities:
-
Authentication: Authentication deals with verifying the identity of the computer sending the data, or the identity of the computer receiving the data. The methods which IPSec can use to authenticate the sender or receiver of data are:
-
Digital certificates: Provides the most secure means of authenticating identities. Certificate authorities (CAs) such as Netscape, Entrust, VeriSign, and Microsoft provide certificates which can be used for authentication purposes.
-
Kerberos authentication: A downside of using the Kerberos v5 authentication protocol is that the identity of the computer remains unencrypted up to the point that the whole payload is encrypted.
-
Pre-shared keys; should be used when none of the former authentication methods can be used.
-
-
Anti-replay ensures that the authentication data cannot be interpreted as it is sent over the network. In addition to authentication, IPSec can provide nonrepudiation. With nonrepudiation, the sender of the data cannot at a later stage deny actually sending the data.
-
Data integrity: Data integrity deals with ensuring that the data received at the recipient has not been tampered with. A hashing algorithm is used to ensure that the data is not modified as it is passed over the network. The hashing algorithms which can be used by IPSec are:
-
Message Digest (MD5); a one-way hash that results in a 128-bit hash which is used for integrity checking.
-
Secure Hash Algorithm 1 (SHA1); a 160-bit secret key to generate a 160-bit message digest which provides more security than MD5.
-
-
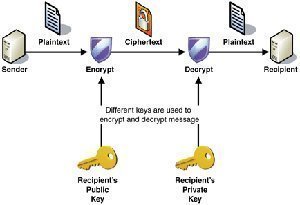
Data confidentiality: IPSec ensures data confidentiality by applying encryption algorithms to data before it is sent over the network. If the data is intercepted, encryption ensures that the intruder cannot interpret the data. To ensure data confidentiality, IPSec can use either of the following encryption algorithms:
-
Data Encryption Standard (DES); the default encryption algorithm used in Windows Server 2003 which uses 56-bit encryption.
-
Triple DEC (3DES); data is encrypted with one key, decrypted with another key, and encrypted again with a different key.
-
40-bit DES; the least secure encryption algorithm.
-
IPSec Policies Summary
IPSec policies are used to apply security in your network. The IPSec policies define when and how data should be secured. The IPSec policies also determine which security methods to use when securing data at the different levels in your network. You can configure IPSec policies so that different types of traffic are affected by each individual policy.
The IPSec policy components are:
-
IP filter; informs the IPSec driver on the type of inbound traffic and outbound traffic which should be secured.
-
IP filter list; used to group multiple IP filters into a single list in order to isolate a specific set of network traffic.
-
Filter action; used to define how the IPSec driver should secure traffic.
-
Security method; refers to security types and algorithms used for the key exchange process and for authentication.
-
Connection type: identifies the type of connection which the IPSec policy impacts.
-
Tunnel setting; the tunnel endpoint's IP address/DNS name.
-
Rule; a grouping of components such as filters and filter actions to secure a specific subset of traffic in a particular manner:
IPSec policies can be applied at the following levels within a network:
-
Active Directory domain; Active Directory site; Active Directory organizational unit; Computers; Applications.
Windows Server 2003 IPSec deployments include predefined IPSec rules, filter lists, filter actions, and three default IPSec policies. Each default IPSec policy contains a set of predefined rules, filter lists and filter actions.
The three predefined IPSec policies are:
-
Client (Respond Only): The Client (Respond Only) default IPSec policy is the least secure predefined policy. Here, the computer assigned the policy never initiates secure data communication. Th computer only responds to IPSec requests from those computers who request it. The Client (Respond Only) predefined IPSec policy contains the default response rule that creates dynamic IPSec filters for inbound and outbound traffic based on the protocol and port which was requested.
-
Secure Server (Request Security): With the Secure Server (Request Security) default IPSec policy, the computer prefers and initiates secure data communication. If the other computer supports IPSec, secure data communication will take place. If the other computer does not support IPSec, the computer will allow unsecured communication with that computer.
-
Secure Server (Require Security): With the Secure Server (Require Security) default IPSec policy only secure data communication is allowed. If the other computer does not support IPSec, the connection is not established.
You can create customized IPSec policies that include customized rules and filters that suit specific security requirements of the organization. You can also create your own IPSec policy by using the IP Security Wizard which you can initiate from within the IP Security Policy Management MMC.
Microsoft Best Practices for Implementing IPSec
The Microsoft best practices for implementing IPSec are summarized here:
-
You need to plan your IPSec implementation and configuration.
-
You should develop a test tab and use the test lab to test the implementation of your IPSec policies. There are a few features of IPSec that are not supported in all versions of the Windows operating systems. Windows Server 2003 does though support all the features of IPSec and it also includes IPSec-specific enhancements.
-
Because preshared keys is considered the least secure supported authentication method, you should only use preshared keys when you cannot use digital certificates or the Kerberos v5 authentication protocol.
-
You should not use the Kerberos v5 authentication protocol for computers that are connected to the Internet. This is primarily because the identity of the computer remains unencrypted up to the point that the whole payload is encrypted.
-
You should use digital certificates as the authentication method for computers that are connected to the Internet. When sending the certificate request, do not however transmit the name of the Certification Authority (CA) together with the request.
-
For computers that are connected to the Internet, only allow secured connections and communication to occur. Ensure that the Allow Unsecured Communication With Non-IPSec Aware Computers option and Accept Unsecured Communication, But Always Respond Using IPSec option is disabled.
-
Diffie-Hellman key agreement enables two computers to create a shared private key that authenticates data and encrypts an IP datagram. IPSec in Windows Server 2003 includes support for the Group 3 2048-bit Diffie-Hellman key exchange which is much stronger and more complex than the previous Group 2 1024-bit Diffie-Hellman key exchange. If you need backward compatibility with Windows 2000 and Windows XP, then you have to use the Group 2 1024-bit Diffie-Hellman key exchange. You should though never use Group 1 768-bit Diffie-Hellman key exchange because it offers the lowest keying strength.
-
If you are running Windows XP and Windows Server 2003 computers, use the Triple Data Encryption Standard (3DES) encryption algorithm which provides the strongest encryption algorithm. When you use 3DES, data is encrypted with one key, decrypted with another key, and encrypted again with a different key. If you running Windows 2000 computers, install the High Encryption Pack or Service Pack 2 so that 3DES can be used.
Securing DNS Infrastructure
The common threats to a DNS infrastructure are:
-
Denial-of-service (DoS) attacks occur when DNS servers are flooded with recursive queries in an attempt to prevent the DNS server fro servicing legitimate client requests for name resolution. A successful DoS attack can result in the unavailability of DNS services, and in the eventual shut down of the network.
-
Footprinting occurs when an intruder intercepts DNS zone information. When the intruder has this information, the intruder is able to discover the DNS domain names, computer names, and IP addresses that are being used on the network. The intruder can then utilize this information to decide on which computers he/she wants to attacks.
-
IP Spoofing: After an intruder has obtained a valid IP address from a footprinting attack, the intruder can use that IP address to send malicious packets to the network, or access network services. The intruder can also use the valid IP address to modify data.
-
A redirection attack occurs when an intruder is able to make the DNS server forward or redirect name resolution requests to the incorrect servers. In this case, the incorrect servers are under the control of the intruder. A redirection attack is achieved by an intruder corrupting the DNS cache in a DNS server that accepts unsecured dynamic updates.
There are a number of by which you can secure DNS servers:
-
If you are using DNS zone files to store zone data, change the zone file permissions or the folder's permissions that stores the zone files to only allow Full Control to the System group.
-
The DNS registry keys stored in HKEY_LOCAL_MACHINESystemCurrentControlSetServicesDNS should be secured as well.
-
If you have a DNS server that is not configured to resolve Internet names, you should configure the root hints to point to those DNS servers hosting the root domain.
-
If you have a DNS server that is not configured with forwarders, and the DNS server does not respond to any DNS clients directly, then it is recommended that your disable recursion for the DNS server.
-
Configure the Secure cache against pollution option to protect the DNS server from an intruder that might be attempting to pollute the DNS cache with the incorrect information.
-
Limit the number of IP addresses that the DNS server listens to for DNS queries
The DNS security recommendations for an external DNS implementation are summarized below:
-
You should harden your DNS servers, and place your DNS servers in a DMZ or in a perimeter network.
-
Ensure that access rules and packet filtering is defined on your firewalls to control source and destination addresses and ports.
-
Install the latest service packs on your DNS servers, and remove all unnecessary services from these servers.
-
Eliminate all single points of failure.
-
Host your DNS servers on different subnets and ensure that your DNS servers have different configured routers.
-
Ensure that zone transfer is only allowed to specific IP addresses.
-
Secure zone transfer data by using VPN tunnels or IPSec.
-
You can use a stealth primary server to update secondary DNS servers which are registered with ICANN.
-
For Internet facing DNS servers, disable recursion, disable dynamic updates, and enable protection against cache pollution
-
Monitor your DNS logs. DNS logging is enabled by default. The DNS service generates DNS logging information that you can use to monitor for attacks on your DNS servers.
Designing Security for Data being Transmitted
Other than IPSec, there are a number of methods which you can use to secure data transmission for a number of different circumstances:
-
Secure Sockets Layer/Transport Layer Security (SSL/TLS) protocol
-
S/MIME
-
Server Message Block (SMB) signing
-
Port Authentication for switches
-
Through segmented networks
Secure Sockets Layer/Transport Layer Security (SSL/TLS) Protocol Overview
The Secure Sockets Layer (SSL) protocol was developed by Netscape Communications to secure communication over the Internet. SSL works at the transport layer of Transmission Control Protocol/Internet Protocol (TCP/IP), which makes the protocol independent of the application layer protocol functioning on top of it. SSL is an open standard protocol and is supported by a range of servers and clients.
SSL can be utilized for the following:
-
To encrypt Web traffic using Hypertext Transfer Protocol (HTTP). When HTTP is utilized together with SSL, it is known as HTTPS.
-
To authenticate Web servers, and to encrypt communications between Web browsers and Web servers.
-
To encrypt mail and newsgroup traffic.
SSL works by combining public key cryptography and secret key encryption to ensure data confidentiality. The Rivest-Shamir-Adleman (RSA) public key algorithm is used to generate the certificates, and the public and private key pairs utilized in SSL. When a client Web browser connects to a Web server that is configured for SSL, a SSL handshake process is initiated with the Web server. The SSL handshake process occurs to negotiate the secret key encryption algorithm which the client and Web server will utilize to encrypt the data which is transmitted in the SSL session.
Transport Layer Security (TLS) is a internet standard version of Secure Sockets Layer (SSL), and is very similar to Secure Sockets Layer version 3 (SSLv3). The key differences between SSLv3 and TLS are:
-
You can extend TLS by adding new authentication methods.
-
TLS utilizes session caching, thereby improving on SSL performance.
-
TLS also distinctly separates the handshake process from the record layer. The record layer holds the data.
The different situations where an SSL/TLS implementation normally occurs:
-
SSL/TLS can be utilized to authenticate client access to a secure site. You can require client and server certificates, and only allow access to the site to those clients that are authenticated.
-
Applications which support SSL can require authentication for remote users logging on to the system.
-
Exchange servers can use SSL/TLS to provide data confidentiality when data is transmitted between servers on the intranet or Internet.
The benefits of implementing SSL/TLS are:
-
SSL/TLS is easy to deploy.
-
Server authentication, and client authentication (optional) occurs.
-
Message confidentiality and integrity are ensured.
-
The parties partaking in the secure session can choose the authentication methods, and encryption and hash algorithms.
The shortcomings associated with deploying SSL/TLS are:
-
SSL/TLS needs additional CPU resources to establish the secure session between the server and client.
-
Because SSL/TLS utilizes certificates, you would need administrators to manage these certificates, and the certificate systems.
S/MIME Overview
Secure /Multipurpose Internet Mail Extensions (S/MIME) can be used to provide end-to-end security for e-mail traffic. You can implement S/MIME to digitally sign e-mail messages being transmitted, thereby protecting the information from being modified.
Digitally signing e-mail messages provides the following key security features:
-
Origin integrity
-
Message integrity
-
E-mail messages can be encrypted as well.
Microsoft Exchange Server 2000 and Exchange Server 2003 support S/MIME. To implement S/MIME, S/MIME requires e-mail application support only. The e-mail servers do not need to support S/MIME.
Server Message Block (SMB) Protocol Signing Overview
Server Message Block (SMB) signing can be implemented to ensure the validity and integrity of data in transit between a client and a server. Server Message Block (SMB) signing can therefore be used to prevent man-in-the-middle attacks. SMB signing ensures the authenticity of a user and the server on which the data resides. To prevent the modification of SMB packets while in transit, SMB supports the digital signing of SMB packets. The signature is then verified at the recipient computer. To sign SMB packets, a mathematical algorithm is run over specific fields within the packet, to calculate a mathematical result. The recipient runs the same mathematical algorithm and then compares the mathematical result. When the two mathematical results match, it means that the data was not modified while in transit. A failure on either the server end or client end results in data not being transmitted.
To protect against the impersonation of clients and servers in high security networking environments that include Windows 2000 based clients and down-level Windows clients, consider implementing SMB signing.
SMB signing is negotiated between the client and the server at the time when the SMB session is established:
-
A client wants to establish a connection with a server that is defined to require SMB signing.
-
The server responds by sending a challenge to the server. The challenge takes the form of the data that the client will encrypt to the server.
-
The client responds by encrypting the challenge with a 168-bit session key. The session key is calculated from the password of the user. Both the response and the actual algorithm which was utilized to encrypt the challenge are sent to the server.
-
The server utilizes its stored value for the user password to carry out the same algorithm on the challenge, and then compares its results to the results received from the client. Authentication of the user occurs when there is a match between the mathematical results.
-
The server and client then negotiate the SMBs version which will be used. The version selected is the highest SMBs version supported by both the server and the client.
-
All messages sent between the client and server is protected through the calculation of a digest. The digest is then included with each message.
When you configure a security template to utilize SMB signing, you can select between the following options:
-
Microsoft network client Digitally sign communications (always)
-
Microsoft network client Digitally sign communications (if server agrees)
-
Microsoft network server Digitally sign communications (always)
-
Microsoft network server Digitally sign communications (if client agrees)
When designing SMB signing security, consider the following factors:
-
By default, server end SMB signing is only enabled on domain controllers. It is not enabled for member servers.
-
By default, client end SMB signing is enabled on domain controllers, servers, and workstations.
-
If you want all communication with a server to require SMB signing;
-
The server must be configured to enable and require the utilization of SMB signing.
-
The client computers have to be configured to enable or require SMB signing.
-
-
If you want communication with a server to allow SMB signing and unsigned communications;
-
The server must be configured to only enable SMB signing.
-
Designing Security for Wireless Networks
The different categories of wireless networks are:
-
Wireless local area networks (WLANs) make it possible for data to be shared within a local area. Wireless bridges connect devices to the wireless network, and can also connect two wireless networks.
-
Wireless metropolitan area networks (WMANs) make it possible to connect buildings in a city. WMANs use either infrared or radio frequency.
-
The second generation of Wireless wide area networks (WWANs) technology is used by cellular phones at the moment. Global System for Mobile Communications (GSM), Cellular Digital Packet Data (CDPD) and Code Division Multiple Access (CDMA) are enterprises that provide WWAN technologies.
-
Wireless personal ara networks (WPANs) connect personal devices so that data can be shared over an area. The personal devices that WPANs connect are devices such as personal digital assistants (PDAs), laptop computers and cellular phones. WPANs can operate using either infrared or radio frequency.
Wireless networks are exposed to the following types of threats are
-
Data modification; data is modified while being transmitted
-
Eavesdropping; data is captured while being transmitted.
-
Denial of service (DoS); the server is flooded with unauthorized requests, making it impossible for the server to service authorized user requests.
-
Spoofing; data is modified so that it looks as though it came from the sender/receiver.
-
Free-loading; network bandwidth is used by an unauthorized individual.
-
Accidental network access; a user with a wireless connection on a device accidentally accesses the network.
-
Rogue wireless networks; authorized users create an unauthorized wireless LAN, connected to the company network.
To secure wireless networks and wireless connections, administrators can require all wireless communications to be authenticated and encrypted. There are a number of wireless security technologies that can be used to protect wireless networks from the different types of attacks that these networks are vulnerable to.
The more common technologies used to protect wireless networks from security threats are:
To provide protection from casual eavesdropping, there are a number of options which WEP provides, including the following:
-
With 64-bit encryption the length of the encryption key defines the degree of encryption that is provided to secure transmissions.
-
128-bit encryption provides greater security than 64-bit encryption.
-
When WEP is configured with the No encryption option, all transmissions are sent in clear text.
A few advantages of using WEP to prevent intruders from examining traffic in transit are listed here:
-
WEP is easy to implement. You only have to configure the encryption key on the APs and your clients.
-
WEP can provide basic security for WLAN applications.
-
Transmission privacy is ensured through RC4 encryption. This means that the shared secret key has to be used for decryption.
-
Transmission integrity is ensured by the CRC-32 checksum.
802.1X authentication uses the Extensible Authentication Protocol (EAP) to provide authenticated communication between the client, the wireless access point (WAP), and a Remote Access Dial-In User Server (RADIUS) service. The Extensible Authentication Protocol (EAP) is a internet Engineering Task Force (IETF) standard protocol. To provide a secure authentication process, the EAP protocol regularly produces a new encryption key. This in turn reduces the vulnerabilities of the WEP protocol.
The authentication components used in the 802.1X authentication process are:
-
EAP-TLS authentication: With EAP-TLS authentication, public key certificates are used to authenticate the RADIUS service, and the client. EAP-TLS authentication is a stronger authentication method than PEAP authentication. To implement EAP-TLS authentication, you need to use a Public Key Infrastructure (PKI).
-
Protected EAP (PEAP) authentication: While EAP-TLS utilizes public key certificates to authenticate clients; PEAP authentication utilizes a user name and password to authenticate clients. EAP-TLS is therefore the stronger authentication method to authenticate wireless clients. One advantage of using PEAP authentication is that it is easy to implement. When PEAP authentication and the RADIUS service are use together, the encryption keys have to be changed on a regular basis. This in turn ensures that WEP encryption cannot be easily broken. The PEAP authentication process has the following two stages:
-
The RADIUS server is authenticated through the examination of its public key certificate. A Transport Layer Security (TLS) session is established between the client and the RADIUS server.
-
An additional EAP method within the PEAP session authenticates the client to the RADIUS service.
-
-
RADIUS service: The RADIUS service is used mainly to authenticate dial-up users, and can be used to authenticate wireless users when they attempt to connect to the network. One of the main benefits of using the RADIUS service is that user authentication for wireless networks are centralized. When a client transmits a request to establish a connection, the RADIUS service verifies the identity of the client by looking for a match in its authentication database. You can also configure a maximum session time limit which forces clients to regularly re-authenticate to the RADIUS service. During re-authentication, a new shared secret is generated, which makes it more difficult for attackers to decipher the shared secret keys.
When designing security for wireless networks, the factors listed below have to be determined or clarified:
-
Determine whether the Wi-Fi Protected Access (WPA) protocol or the Wired Equivalent Privacy (WEP) protocol will be used.
-
If you select to use the WAP protocol, determine whether your hardware needs to be upgraded to support WPA.
-
If you select to use the WEP protocol, determine whether 64-bit or 128-bit encryption will be used.
-
Determine whether 802.1X authentication will be used.
-
Determine whether wireless clients will use IPSec.
-
Determine whether MAC address filtering will be used to limit wireless access based on MAC addresses.
-
Determine whether Group Policy will be used to configure wireless client security settings; or whether it will be manually configured.
-
Determine whether your wireless network security strategy involves monitoring of wireless network activity, and if yes, how and when will you monitor wireless network traffic.
Maintaining a Security Plan
The typical circumstances under which a security plan should be updated are summarized here:
-
A change occurs to the existing organizational structure.
-
There is a change in the existing security policy or strategy of the organization.
-
Microsoft issued a new security update to deal with a security threat.
-
Mergers and takeovers usually mean an expansion or complete modification of existing security plans.
One of the challenges you face when designing network infrastructure security is to maintain an already implemented security plan. This is necessary to ensure that your existing security plan remains current, valuable and effective.
-
To keep updated on all new security threats;
-
Regularly reference network security Web sites.
-
Subscribe to security bulletins.
-
-
To keep up to date on all released security fixes;
-
Apply all the latest hotfixes and service packs to computers.
-
Reference the Microsoft Web site to check your system for missing security fixes.
-
-
To make certain that the security plan is based on the security policy;
-
Regularly update the security plan when modifications are made to the security policy of the organization.
-
Regularly examine the security plan to ensure that it is still based on the security policy.
-

Follow Us!