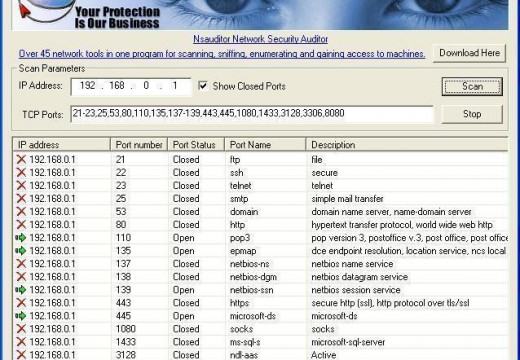
Packet sniffing is listening (with software) to the raw network device for interesting packets. When the software sees a packet that fits certain criteria, it logs it to a file. The most common criterion for an interesting packet is one that contains words like “login” or “password.”
To packet sniff, obtain or code a packet sniffer that is capable of working with the type of network interface that the operating system supports:
Network interfaces include:
- LLI
- NIT (Network Interface Tap)
- Ultrix Packet Filter
- DLPI (Data Link Provider Interface)
- BPF (Berkeley Packet Filter)
LLI was a network interface that SCO used, which has been augmented with DLPI support as of SCO OpenServer Release V.
NIT was a network interface that Sun used, but has been replaced in later releases of SunOS/Solaris with DLPI.
Ultrix supported the Ultrix Packet Filter before Digital implemented support for BPF.
DLPI is supported under current System V Release 4 releases, SunOS/Solaris, AIX, HP/UX, UnixWare, Irix, and MacOS. DLPI is partially supported under Digital Unix. Sun DLPI version 2 supports Ethernet, X.25 LAPB, SDLC, ISDN LAPD, CSMA/CD, FDDI, Token Ring, Token Bus, and Bisync as data link protocols. The DLPI network interface provided with HP/UX supports Ethernet/IEEE 802.3, IEEE 802.5, FDDI, and Fibre Channel.
BPF is supported under current BSD and Digital Unix releases and has been ported to SunOS and Solaris. AIX supports BPF reads, but not writes. A BPF library is available for Linux.
Packet Sniffers
Commercial, bundled, and free packet sniffers are available for most operating systems:
Free Packet Sniffers
Ethereal
Platform(s): Most
License: Open Source GPL
Network professionals around the world use Ethereal for troubleshooting, analysis, software and protocol development, and education. It has all of the standard features expected in a protocol analyzer and several features not seen in any other product. Its open source license allows talented experts in the networking community to add enhancements. It runs on all popular computing platforms including Unix, Linux, and Windows.
tcpdump
Platform(s): Most
License: BSD License
Tcpdump prints out the packet headers on a network interface that match the boolean expression. It can also be run with the -w flag, which causes it to save the packet data to a file for later analysis, and/or with the -b flag, which causes it to read from a saved packet file rather than to read packets from a network interface. In all cases, tcpdump will only process packets that match expression.
nfswatch/
Platform(s): Unix
License: Open Source
nfswatch is a packet sniffer that is dedicated to sniffing NFS (Network File System) traffic. nfswatch lets users monitor NFS requests to any given machine or the entire local network. It mostly monitors NFS client traffic (NFS requests). It also monitors the NFS reply traffic from a server in order to measure the response time for each RPC.
Sniffit
Platform(s): Linux, SunOS, Solaris, FreeBSD and Irix
License: Open Source
sniffit is a packet sniffer for TCP/UDP/ICMP packets. sniffit gives very detailed technical info on these packets (SEQ, ACK, TTL, Window, …) and packets contents in different formats (hex or plain text, …).
Bundled Packet Sniffers
Microsoft Network Monitor
Platform(s): Windows
License: Bundled with Microsoft Windows
Microsoft Network Monitor is the packet sniffer that is bundled with Microsoft Windows.
Network Monitor is a Microsoft Systems Management Server (SMS) component that enables users to detect and troubleshoot problems on LANs, WANs, and serial links running the Microsoft Remote Access Server (RAS). Network Monitor provides real-time and post-capture modes of network data analysis.
In real-time analysis, real-time monitors examine network traffic. These monitors test network traffic for a specific set of conditions and display events when those specific conditions are detected, which may prompt end-user action. For example, a monitor can detect conditions that indicate a SYN attack and aid a network administrator to respond to the potential attack.
In post capture analysis, network traffic is saved in a proprietary capture file so that the captured data can be analyzed later. In this case, analysis can be in the form of protocol parsers picking out specific network frame types and displaying the frame data in the Network Monitor UI. Also, analysis can be in the form of experts examining the network data and displaying a report (experts may also manipulate the network data).
Network Monitor provides the following functions:
- Captures network data in real-time or delayed mode.
- Provides filtering capabilities when capturing data.
- Uses monitors for real-time analysis and security.
- Uses experts and parsers for detailed post-capture analysis.
snoop
Platform(s): Solaris
License: Bundled with Solaris
snoop is the packet sniffer that is bundled with the Solaris Operating System.
snoop captures packets from the network and displays their contents. snoop uses both the network packet filter and streams buffer modules to provide efficient capture of packets from the network. Captured packets can be displayed as they are received or saved to a file for later inspection.
snoop can display packets in a single-line summary form or in verbose multi-line forms. In summary form, only the data pertaining to the highest level protocol is displayed. For example, an NFS packet only displays NFS information. The underlying RPC, UDP, IP, and Ethernet frame information is suppressed, but can be displayed if either of the verbose options are chosen.
nettl / netfmt
Platform(s): HP-UX
License: Bundled with HP-UX
The nettl and netfmt packet sniffing utilities are bundled with the HP-UX operating system.
Commercial Packet Sniffers
LanWatch
Platform(s): DOS/Windows
License: Commercial
LANWatch is a software based network packet analyzer. Easy to install and use, LANWatch monitors traffic in real time and displays a wide range of statistics. With LANWatch, network administrators can quickly identify problems and keep networks running at peak performance. Support and QA Personnel can determine the network problems’ origin. Network Application and Protocol Developers can easily monitor, examine, and verify network protocols in both hexadecimal and formatted views.
Etherpeek
Platform(s): Windows, Macintosh
License: Commercial
EtherPeek is an Ethernet network traffic and protocol analyzer designed to make the complex tasks of troubleshooting and debugging mixed-platform, multi-protocol networks easy. EtherPeek sets the industry standard for easy use while delivering all the superior diagnostic and analysis capabilities expected of a full featured analyzer at an affordable price.
EffeTech HTTP Sniffer
Platform(s): Windows
License: Commercial
EffeTech HTTP Sniffer is an HTTP packet sniffer, protocol analyzer, and file reassembly software based on a Windows platform. Unlike most other sniffers, it is dedicated to capturing IP packets containing HTTP protocol, rebuild the HTTP sessions, and reassemble files sent through HTTP protocol. Its smart real-time analyzer enables on-the-fly content viewing while capturing, analyzing, parsing, and decoding HTTP protocol.
Iris
Platform(s): Windows
License: Commercial
Iris is a powerful, yet intuitive network traffic analyzer that allows system administrators to examine their network’s inner workings, simplifying the detective work of pinpointing a security breach or resolving a performance problem.
Iris takes network traffic and returns it to its original format, dramatically reducing the time previously spent examining individual packets. Utilizing Iris, security professionals are able to read an email’s actual text as well as any attachments exactly as it was sent, reconstruct the actual HTML pages that the users visited, and even simulate cookies for entry into password protected websites.
Iris provides automated filters that can be set up to flag and record specific network traffic that contains a particular MC or IP address, unacceptable words or websites, etc., to ensure whether company security is being compromised or corporate policies are abused. Iris also provides a variety of statistical measurements, allowing users to proactively identify and take the steps to eliminate performance issues before they can result in downtime.

mark
What troubleshooting task will a packet sniffer NOT helpwith
lakshmi
i need simple source code for program to capture packets using sniffer using c in unix
lakshmi
i need a source code for program to capture packets using sniffer using c in unix
sylviya
detail about this title
eran
Hello
Can anyone help me.
I have to code (no matter what language), showing the traffic on your computer – that is when I surf the Internet code shows me all the traffic of the computer to the Internet and back.
If you can send email erana@lnts.com
Thank you
siddu
thanks for the info..