To audit Unix passwords, you must compare each encrypted password in the Unix password file with a set of potential encrypted passwords. These potential encrypted passwords are created by encrypting every password in a list of plaintext passwords. This is an example of a dictionary attack.
The Unix passwd File Location
The traditional location for the Unix password file was /etc/passwd.
Unix password file format
An entry in the Unix password file consists of seven colon delimited fields:
Username Encrypted Unix password (And optional password aging data) User number Group Number GECOS Information Home directory Shell
Sample entry from /etc/passwd:
will:5fg63fhD3d5gh:9406:12:Will Spencer:/home/will:/bin/bash
Broken down, this passwd file line shows:
Username will Encrypted Unix password 5fg63fhD3d5gh User number 9406 Group Number 12 GECOS Information Will Spencer Home directory /home/will Shell /bin/bash
Auditing Unix passwords
Contrary to popular belief, Unix passwords cannot be decrypted. Unix passwords are encrypted with a one way function. The login program accepts the text you enter at the “Password:” prompt and then runs it through a cryptographic algorithm. The results of that algorithm are then compared against the encrypted form of your Unix password stored in the password file.
On a more technical level, the password that you enter is used as a key to encrypt a 64-bit block of NULLs. The first seven bits of each character are extracted to form a 56-bit key. This means that only eight characters are significant in a standard Unix password. The E-table is then modified using the salt, which is a 12-bit value, coerced into the first two chars of the stored password. The salt’s purpose is to make precompiled password lists and DES hardware chips more time consuming to use. DES is then invoked for 25 iterations. The 64-bit output block and is then coerced into a 64-character alphabet (A-Z,a-z,”.”,”/”). This involves translations in which several different values are represented by the same character, which is why Unix passwords cannot be decrypted.
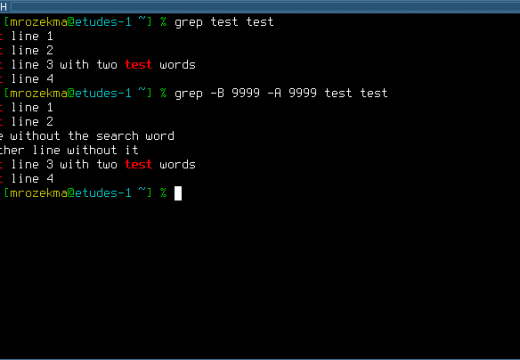
Unix password auditing software uses wordlists to implement a dictionary attack. Each word in the wordlist is encrypted using the algorithm described above and the salts from the password file. The results are then compared to the encrypted form of the target password.
To audit Unix passwords under Unix or DOS/Windows, try John the Ripper. For the Macintosh, try Killer Cracker or Mac Krack.
Password Shadowing
Password shadowing is a security system where the encrypted password field of /etc/passwd is replaced with a special token and the encrypted password is stored in a separate file (or files) which is not readable
by normal system users.
The getpwent() Unix Password Shadowing Vulnerability
On older Unix systems, password shadowing was often defeated by using a program that made successive calls to getpwent() to obtain the entire password file. Modern Unix systems are not susceptible to this attack.
Example:
#include <pwd.h>
main()
{
struct passwd *p;
while(p=getpwent())
printf("%s:%s:%d:%d:%s:%s:%sn", p->pw_name, p->pw_passwd,
p->pw_uid, p->pw_gid, p->pw_gecos, p->pw_dir, p->pw_shell);
}
Unix Password Shadowing on Various Unix Implementations
Some Unix password shadowing schemes store the shadowed passwords in a single file, while others utilize a hierarchy of multiple files.
Token is the text placed in the second field the /etc/passwd file.
| Unix | Path | Token |
|---|---|---|
| AIX 3 and AIX 4 | /etc/security/passwd or /tcb/auth/files/<first letter of username>/<username> |
!# |
| A/UX 3.0s | /tcb/files/auth/?/* | |
| BSD4.3-Reno | /etc/master.passwd | * |
| ConvexOS 10 | /etc/shadpw | * |
| ConvexOS 11 | /etc/shadow | * |
| DG/UX | /etc/tcb/aa/user/ | * |
| EP/IX | /etc/shadow | x |
| HP-UX | /.secure/etc/passwd | * |
| IRIX 5 | /etc/shadow | x |
| Linux 1.1 | /etc/shadow | * |
| OSF/1 | /etc/passwd[.dir|.pag] | * |
| SCO Unix 3.2.x | /tcb/auth/files/<first letter of username>/<username> | * |
| SunOS4.1+c2 | /etc/security/passwd.adjunct | ##username |
| SunOS 5.0 / Solaris 2.x | /etc/shadow or Optional NIS+ private secure maps |
|
| System V Release 4.0 | /etc/shadow | x |
| System V Release 4.2 | /etc/security/* database | |
| Ultrix 4 | /etc/auth[.dir|.pag] | * |
| UNICOS | /etc/udb | * |

Follow Us!