GPG, or GNU Privacy Guard, is a free replacement and competing product for PGP (Pretty Good Privacy). The project is a data encryption and decryption application which provides end-users with a cryptographic privacy and authentication system for communicating electronic data. GPG can be used to sign, encrypt, and decrypt text, for email, files, directories, and entire disk partitions. It is primarily intended to increase the security of email communications similar to PGP; however, is a completely free implementation of the OpenPGP standard.
What is the OpenPGP Standard?
OpenPGP is the non-proprietary protocol created to allow encrypting email using public key cryptography technology. The protocol is based on the PGP work created by Phil Zimmermann and defines the standard formats for exchanging public keys, encrypting messages, certificates, and signatures.
In 1997, the OpenPGP Working Group was formed under the IETF (Internet Engineering Task Force) to create an open source standard. Previous to the formation of the working group, the standard had existed as a proprietary product since 1991. By publishing the results of the working group as an IETF proposed standard under RFC 4880, OpenPGP is now able to be implemented by any company or organization without having to pay any licensing fees.
What is the OpenPGP Alliance?
The OpenPGP Allience is an organization that allows companies to collaborate with a common goal – to produce and promote a consistent international standard for email encryption. This work applies the PKI methodology and thought processes that have emerged from the OpenPGP community to applications other than email. By participating in the OpenPGP Alliance, members are able to join a team of developers and businessmen and women who are able to work together on both the current standard and future modifications or improvements as technology improves. As a result, OpenPGP has become the leading standard for public key cryptography in the past decade.
What is GnuPG?
GnuPG is the open source implementation of the OpenPGP standard as defined by the IETF’s RFC 4880. GnuPG (or GPG) allows consumers and developers to both encrypt and sign data and standard communications. The project includes a versatile key management system in addition to access modules for a number of public key directories. There are a number of applications and libraries included with the GPG distribution. The second version of GPG (GnuPG) also includes support for S/MIME. At the time of this writing, there are two production versions of GnuPG (GPG) in release:
1.4.13 which is the standalone, portable version of the distribution and most used, and
2.0.19 which is the most enhanced version of the project, but can be more challenging to build.
All versions of GnuPG are open source, or free. One is allowed to use, modify, and distribute GPG in accordance with the GNU General Public License.
How Does the GNU General Public License Work?
The GNU GPL (GNU General Public License) is the most used free software license in the market. The license ensures that the end-user (defined as an individual, company, or organization) has the freedom to both use, share, copy, or study the software produced under the license. Any software application or project produced under this license ensures the software remains free. The original GNU GPL was written by Richard Stallman from the FSF (Free Software Foundation) for the GNU project.
When a computer program, application, or other software project is published under the GPL, the Free Software Definition rights are transferred to the user of the project. Additionally, copyleft is included in the GPL to help ensure that these freedoms remain in-tact when the work is distributed. The terms also include derivative works created from the originally published work.
Since the GPL is a “copyleft” licsense, it ensures that derivative works can only be distributed under the same terms. This fact makes GPL-based work distinct from other open source licenses such as BSD. GPL was the first copyleft license published for general use and the third version of the GPL was released on June 29th, 2007. In order to ensure the license implementation remains “Up-To-Date,” the GPL includes a “any later version” clause that allows users of the software to choose between the original or new terms as they are revised by the FSF. Developers are also free to delete this clause in the event they don’t want to have the terms of the license changed post-production.
GPG History
The GPG (GnuPG) project was originally created by Werner Kock. He released version 1.0.0 on September 7th, 1999. In 2000, the German Federal Ministry of Economics and Technology funded the port of the project to Microsoft Windows and the associated documentation. Since the GnuPG project is compliant with the OpenPGP standard, it was also designed to interoperate with PGP. The second version of GPG was released on November 13th, 2006. The original 1.x branch of the project will continue to be developed in parallel with the GnuPG 2 series due to the number of changes in the architecture of the program in the new version.
GnuPG Usage in Industry
The basic GPG implementation includes a command line interface. There are a number of front-end applications that provide a GUI (graphical user interface) for use with the program. As an example, KMail and Evolution email clients include GPG encryption support in the email clients (these programs are included in the Linux KDE and GNOME desktops). There are also a number of GPG GUI front-end clients to include KPGP for KDE and Seahorse for GNOME.
Not to be left out, Mac OS X users are able to implement a number of Aqua front-end applications for encryption and key management using the Mac GPG project builds (MacGPG). The instant messaging programs such as Fire and Psi are also capable of securing messages when GPG is installed and property configured on a client computer.
The web-based software application, Horde, also provides the ability for end-users to make use of GPG. For those who like to use SeaMonkey and Mozilla Thunderbird, Enigmail provides GPG support for these applications as well as Mozilla Firefox. Fire GPG support was discontinued on June 7th, 2010.
In 2005, Gpg4win was released by G10 Code and Intevation. This release included a software suite to support common applications on the Microsoft Windows platform to include Windows Explorer and Microsoft Outlook. Specific tools included Gnu Privacy Assistant and GnuPG for Windows.
How Does GPG Work?
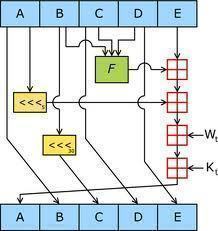
GPG encrypts messages created by the end-user. The application does this by leveraging asymmetric keypairs which are created by each GnuPG user. The end result is a public key that can be exchanged with other end-users via a variety of methods to include Internet key servers. The keys must be exchanged in a cautious manner; however, in order to prevent nefarious users from spooking the identity of others through the act of corruption the public key owner identity correspondence.
GPG also makes it possible for an end-user to add a cryptographic signature to a message to ensure that both the sender’s identity and message identity can be verified. The software package also includes symmetric encryption support. The system also uses the CASTS5 symmetrical algorithm by default. In GnuPG, there is no use of restricted software, algorithms, or patented systems such as those found in PGP.
To provide the maximum flexibility to the end-user, GPG does make it possible to download and use the IDEA encryption algorithm used in PGP. If one does this; however, he or she may be susceptible to having to pay license fees. The non-patented encryption algorithms used in GnuPG include:
CAST5, Camellia, Triple DES, AES, Blowfish, and Twofish.
GPG Supported Asymmetric-key ciphers: ElGamal and RSA
GPG Supported Cryptographic hashes: RIPEMD-160, MD5, SHA-1, SHA-2, and Tiger
GPG Supported Digital signatures: DSA and RSA
Since GPG is a hybrid encryption software application, it allows the use of conventional symmetric-key cryptography when speed is the priority. PKI is leveraged for the ease of use for exchanged secure keys and relies on using the intended recipient’s public key to encrypt a one-time-only session. This type or mode of operation has been included as part of PGP since its original publication.
Problems with PGP
There are several issues with the PGP implementation. First, there are a number of methods available in the OpenPGP standard to digitally sign messages. Due to an error in a change made to GnuPG to make one of the methods more efficient, a security vulnerability was introduced to the project in 2003. Although the error only impacted a single method of digitally signing messages and only for some releases of the project, the damage caused appeared to be minimal. Support for the method was removed from subsequent released of GnuPG after the discovery (1.2.4 and later).
There were two additional vulnerabilities to GPG disclosed in the early portion of 2006. The first was found with scripted instances or uses of GPG verification resulting in some false positive results. The second instance dealt with non-MIME messages being vulnerable to the injection of information when not part of the digital signature. These cases would then be reported as being part of the signed messages. In each of these cases, updated versions of GPG were immediately made available to the public at the time of announcement of the vulnerabilities.
Finally, since GnuPG is a command-line based “system” or “program” and not an API, it can be a tad cumbersome or tedious to include the work into larger applications. GPGME is an API “wrapper” developed around the GnuPG application that will then parse the output of GnuPG and provide to a front-end or other program making a GPGME API call. Since GPGME makes use of a unique GnuPG interface designed for “machine” and not human use, it is considered to be a maintainable API between software components. Potential security issues doe exist in applications that do not propagate to actual cryptographic code due to the computer process barrier that is present.
How to Install and use GPG on Windows?
Step 1 – Install GPG and the GPG Shell. The software is produced by Roger Sondermann.
Step 2 – Download the most current version of WinPT to your computer. The installation is designed to not change dependencies on the Windows OS and is crafted to be uninstalled in a straightforward manner.
Step 3 – Download the precompiled binaries of the GPG build to the computer’s hard drive. Ensure the binaries are placed in their own folder on the drive.
Step 4 – After the files have downloaded, double-click the executable file that was downloaded.
Step 5 – Select the “Yes” menu button when prompted with the display message, “Do you want to start GPG Preferences?”
Step 6 – Select or use”c:\Apps\GPG” for all preferences when installing the application.
Step 7 – In the computer’s system tray, right click the WinPT icon.
Step 8 – Generate a new GPG key for use by selecting “GnuPG / Key Generation” menu option. You will want to select the maximum key size to ensure optimal security.
Step 9 – To encrypt text messages, use the clipboard to encrypt / sign and decrypt / verify information. There is also functionality for conducting operations on full files that can be attached normally to email once GPG has encrypted the information.
Step 10 – Exchange public keys with intended recipients before you start sending or receiving encrypted email. You will have to have one’s public key to encrypt email to send to them. Conversely, they will also need your public key to send encrypted email to yourself.
Step 11 – Exit and then restart the WinPT application after executing key management features. This will help clear the cache in the application to avoid any potential issues when using PGP.


mito cruz
hi . I have a concern. am working in one of the departments of a bank. I suspect that my co workers are viewing my pc / remotely accessing my Pc while am working. a winvnc is installed in my pc. how can i prove that my pc is being remotely accessed by another co worker? thank you. mito