Malware is a generic term for bad software. The word malware comes from the words malicious and software.
Malware (Malicious Software) is software conceived to gain access to a computer without the end user’s knowledge or permission. Malware in general, pertains to a wide range of malicious software that includes computer viruses, Trojan horses, fraudulent adware, spyware, crimeware and so on. According to certain studies, malware is produced at such a high rate that it may even be more than that of genuine software applications.
Prior to the advent of the Internet, viruses were proliferated on computers by contaminating programs or boot sectors of floppy disks. Worm programs were first distributed on Unix based systems. The first virus programs were built for research purposes or as pranks. Today malware programs are distributed primarily via the Internet and e-mail.
Types of Malware
Types of malware include:
- Computer viruses
- Computer worms
- Trojan horses
- Logic bombs
- Spyware
- Adware
- Spam
- Popups
Trojan Horses
A Trojan horse is a type of malware that disguises itself as a required program and requests the user to install it; however it actually enables unapproved remote access to the user’s computer. It can be used for data theft, removal of files, uploading of files, downloading of files, alteration of files and so on. Recent examples of Trojan horses are Mocmex, Torpig, and Conflicker.
Rootkits
A rootkit is a type of malicious software program that helps in masking the actuality that a computer has been infected or is vulnerable. Rootkits change critical operating system files and executables in order to protect files and processes installed by the hacker. It may also install a back door to the computer for future access. Firmware, kernel, application, library and hypervisor level kits are the different types of rootkits.
Backdoors
A backdoor is a technique that is used by other malware to evade preset authentication processes. After a computer is infected by another malware, backdoors are set up to permit effortless access in the future.
Spyware
Spyware programs are created specifically for the purpose of collecting information and data about computer end-users. It uses the collected information and data for the commercial benefit of its creator. Based on a user’s web browsing pattern, spyware can manipulate search engine results to display paid advertisements. At times a user’s computer can be used by spyware to send out spam messages.
Key Logger
Key loggers are used to catch a user’s keystrokes when typing a password, credit card number, web site login credentials, or any other type of personal information for deceptive manipulation. Such information is sent to the creator of the malware for fraudulent use.


Patsi Lewis
Every time I get on this computer, it tells me that it has blocked something, even though I have not started reading or typing. HELP!
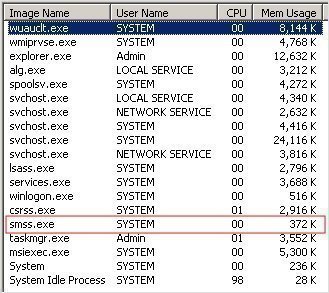
Daniel Memetic
It is possible that there are background processes which are trying to access something online, but are being blocked by your firewall or antivirus application. You can see all the running processes by pressing ctrl-alt-delete and launching the Task Manager to see if there’s anything suspicious, but it’s best for someone computer savvy to look at this. A more thorough scan with an up-to-date antivirus program might be a good idea too.