The XOR encryption is a simple symmetric cipher that is used in many applications where security is not a defined requirement.
The XOR Operator
XOR (Exclusive OR) is a bitwise operator from binary mathematics.
The six bitwise operators, as defined in the C programming language, are:
Operation Symbol AND & Inclusive OR | Exclusive OR (XOR) ^ Right Shift >> Left Shift << Complement ~
The XOR operator returns a 1 when the value of either the first bit or the second bit is a 1.
The XOR operator returns a 0 when neither or both of the bits are 1.
This is best illustrated in the following chart:
First Bit Second Bit Result 0 0 0 0 1 1 1 0 1 1 1 0
The XOR operator is used to “flip” bits (zeroes and ones) in a piece of plaintext to create a ciphertext.
Converting Plaintext to Ciphertext with XOR Encryption
The plaintext being started with is the term “FAQ.”
- ASCII representation of the plaintext: FAQ
- Hexadecimal representation of the plaintext: 70 65 81
- Binary representation of the plaintext: 01110000 01100101 1000000
XOR the first character of this plaintext into ciphertext using a “V” as the key:
- ASCII representation of the key: V
- Hexadecimal representation of the key: 56
- Binary representation of the key: 10000110
Plaintext ‘F’ Key ‘V’ Ciphertext 0 1 1 1 0 1 1 0 1 1 0 1 0 0 0 0 1 1 0 0 0 0 1 1
Converting Ciphertext to Plaintext with XOR Encryption
XOR encryption is a symmetric algorithm. This means that the encryption key can be used as the decryption key.
Decrypt the ciphertext to recreate the original plaintext.
Ciphertext Key ‘V’ Plaintext 1 1 0 1 0 1 1 0 1 1 0 1 0 0 0 1 1 0 0 0 0 1 1 0
Users should do the math themselves with the other two characters of plaintext to prove this to themselves.
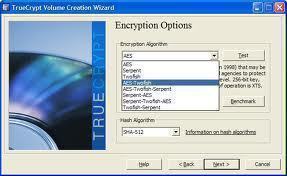
Many encryption algorithms utilize the XOR operator as part of their operations.
Understanding XOR and the other binary operators is a necessary step on the path to becoming a cryptologist.
XOR Security
XOR encryption is simple to implement and equally simple to break.
XOR encryption should not be utilized for any data that the user wants to protect.


Rachel
Small error: The hex representation of “v” is actually 56, not 86. 86 is the decimal representation.
admin
Indeed. Fixed.Thank you.
Naveen
converting plain text to cipher text with XOR Encryption in these topic the ASCII representation of the key is v and the binary representation you used first is 10000110 but in the table you used 10000101.For what reason you changed the key in table
Daphne
And I think your plaintext F is actually the representation of p. Can you double-check your work? If I am on the right track, you used the hexadecimal 70, where it should be the decimal.
Daphne
It looks like there is an error on this page. The binary representation of V (134) looks incorrect in the table format. Can you double-check? If there is a 1 in the last spot, it cannot be even.
Dezmats
So how you brake it ? exemple. Yahoo .dat files are encrypted with XOR. right?