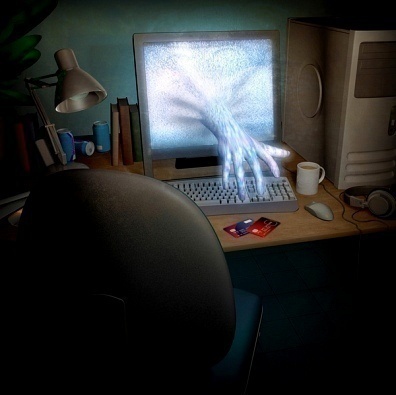
Why People Write Computer Viruses?
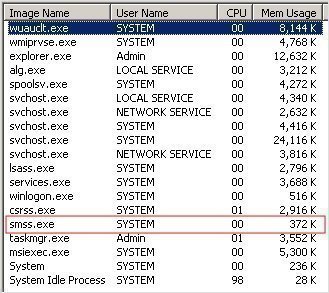
We hear about new computer viruses all the time. What is the motivation behind developing computer viruses and watching them wreak havoc on the Internet? Fact Gathering Many viruses raid your documents including your email address book for information that can be used to make business contacts. This data is assembled into a database that …