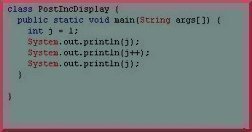
Java Data Types
Data types in the Java programming language are basically divided into two groups – primitive data types and object references. A primitive data type is a basic building block and has full built-in support. Many other languages also support composite data types, which are build on a combination of primitive data types and may or …