Internet Connectivity Introduction
In most organizations and networks today, Internet connectivity is no longer an additional option, but a necessity. Most organizations that have a networking environment need to provide its employees or users with some form of connectivity to the Internet.
E-mail and Web sites have evolved into being important mechanisms for a vast number of organizations. Internet connectivity or connections support a company's business in a number of ways. Company employees use the Internet for a number of reasons, including the following:
-
Exchange e-mail with other employees at different branch offices, and with business partners and suppliers.
-
Access the LAN when working from home.
-
Find valuable information, or conduct research using the Web
-
Mobile users utilize the Internet to remotely access the LAN.
-
The Internet also provides the means for other organizations to connect to the company to perform business transactions.
The importance of the Internet to organizations has made developing and implementing the best strategy for connecting the organization's network to the Internet, an important function for most organizations. Developing and enforcing a policy that deals with implementing and managing Internet connections of the organization is no longer an unimportant, unnecessary task.
Typical issues that need to be clarified before Internet connections can be implemented, maintained, and managed include the following:
-
What method will be utilized to provide the company's network with Internet connections and Internet access.
-
What quantity of Internet access is required.
-
What security measures and mechanisms need to the used and implemented to secure the private internal network from unauthorized access.
-
What measures will be used to allow certain Internet users and VPN users access to specific resources on the private network.
There are a number of mechanisms and features provided by Microsoft that enable you to implement Internet connections. Understanding the available technologies and mechanisms, and the degree of Internet connectivity and security provided by each different method, is important. Connecting the LAN to the Internet can be achieved through translated connections using Network Address Translation (NAT), or through routed connections. To connect branch offices and to make the organization's network accessible from remote locations, virtual private networks (VPNs) and router-to-router VPNs can be utilized. Demand-dial connections or persistent connections can be used. The Point-to-Point Tunneling Protocol (PPTP) VPN tunneling protocol or the Layer 2 Tunneling Protocol (L2TP) VPN tunneling protocol can be used to establish VPN connections. Remote access policies can be used to manage your VPN connections, and secure these connections. Authentication and encryption methods can be used to secure VPN connections. Also, Internet Authentication Service (IAS) can be used to provide centralized user authentication, authorization, and accounting and auditing. IAS can be integrated with the Remote Access and Routing Service (RRAS) of Windows Server 2003.
To connect a network or the LAN to the Internet, you can use either of the following method:
-
A router which routes traffic to the Internet, and from the Internet.
-
A translation service such as Network Address Translation (NAT) to translate private internal network traffic to public traffic which can be routed on the Internet.
Steps by Step Guide for Connecting the Company to the Internet
Before a company can connect to the Internet, certain elements and mechanisms have to be in position. This section of the Article merely provides a quick reference guide for connecting the company to the Internet s that employees, and business partners and clients can make use of the Internet for e-mail, and to conduct business transactions:
-
Determine what the business requirements are for Internet connectivity for the specific organization. There may be instances where the organization needs to host its own Web site or e-mail; and then there may be occasions where this can be provided by a third-party entity. Determine whether demand-dial connections or persistent connections will be used.
-
Determine the type of connections which will be used, that is, routed connections or translated connections.
-
Obtain an active link to the Internet from a internet Service Provider (ISP), and if necessary, obtain a static IP address or range of IP addresses.
-
Obtain the necessary networking devices such as remote access devices, routers, and a firewall solution if necessary. The requirements of the organization will dictate the networking devices which need to be utilized.
-
Configure the IP address for the public network on the public network interface of the router. Configure the IP address of a subnet within the internal private network on the private interface of the router.
-
Determine the domain name which will be used for the organization. The domain name has to be registered with a recognized domain registrar. For the top-level domain, use .com or .biz if you are a company. .org should be used if you are a non-profit organization. All companies that want to do business through the Internet must have domain name. There are a number of approved domain registrars that can register the domain name that you select.
-
Ensure that the registered domain name resolves to the IP address which will be used for Web sites and e-mail. The registered domain name can also be utilized internally with the Active Directory directory service.
-
The next step is to implement network security and firewall solutions to secure the gateway between your private internal network and the public network. The nature and security requirements of the company will influence the level of security that need to be implemented.
-
Set up the clients on the private internal network to use the gateway to establish a connection to the public network or Internet. You can do this through manual configuration, or you can utilize the Dynamic Host Configuration Protocol (DHCP) service to do this.
-
Additional post Internet connection establishment steps include implementing a proxy server, port forwarding, auditing, and so forth.
Understanding Routed Connections to the Internet
A routed connection to the Internet utilizes a routing device or router to pass traffic between the private network and the public network or Internet. A router essentially routes traffic to the Internet, and from the Internet.
Using routers to route traffic between the private network and Internet has the following features and characteristics:
-
Enables full Internet access for all computers located on the private network.
-
Enables all computers on the private network to access the Internet to provide services such as Domain Name System (DNS) to the Internet.
The different types of routers are:
-
Hardware routers: These are dedicated routing devices thats sole purpose is to provide a routing capability for the organization. Hardware routers are ideal for providing Internet connections for the organization.
-
Software routers: Software routers run as a service on a computer residing within the network. The requirements for a computer to run as a software router are:
-
A connection to the internal private network or LAN.
-
A connection to the public network or Internet.
The Routing and Remote Access Service (RRAS) of Windows Server 2003 can be used to enable a computer to run as a software router.The computer running as a software router with the necessary connections is called a multi-homed network computer.
-
Before computers located on the LAN can use a routed connection to connect to the Internet, the following events has to occur:
-
Obtain valid IP addresses from a internet Service Provider (ISP). These addresses are in turn obtained from and managed by an approved authority.
-
Assign these valid IP addresses to computers residing in the private network using either of the following methods:
-
Manually configure the necessary computers with IP addresses.
-
Use the Dynamic Host Configuration Protocol (DHCP) service to do this. Here, you will need to configure the IP addresses on the DHCP server which the DHCP server can then assign to DHCP clients.
-
A few advantages of using routed connections to connect the LAN to the Internet are summarized below:
-
Setting up routed connections is easy because you typically only need a simple hardware implementation.
-
Routed connections provide full Internet connections for all computers residing within the private network.
-
Because the routers provide the Internet connections, these connections are maintained and upheld even when the other network servers are unavailable.
-
All multimedia applications usually work with a routed connection. This is not always the case with translated connections to the Internet.
-
Because a computer has a dedicated IP address for the Internet, it can be used for providing services such as Domain Name System (DNS) to the Internet.
The main disadvantages of using routed connections to connect the LAN to the Internet are listed here:
-
A different IP address is needed for each computer within the private network that needs to access the Internet.
-
Computers within the LAN can be accessed from the Internet, and from anywhere. This could lead to a number of security issues.
Understanding Translated Connections to the Internet
A translation service can be used to translate private internal network traffic to public traffic which can be routed on the Internet. When you use translation services, all computers on the LAN can connect to the Internet through a single public IP address. Also, the private network is not directly accessible by Internet users as is the case with routed connections.
The Network Address Translation (NAT) translation service can be used to translate internal addresses to public addresses which can be routed on the Internet.
The computer performing the role of the NAT server has the following requirements:
-
One network adapter card configured with the internal private IP addresses connecting the internal private client computers.
-
One network adapter configured with the public IP address which connects to the Internet.
Windows supports two implementations of the NAT service:
- Windows 2000 Server
- Windows Server 2003
Internet Connection Sharing (ICS); should be used for very small networks only. ICS can be considered a simplified basic version of NAT. Internet Connection Sharing (ICS) is a service integrated with Windows that provides Internet connectivity to hosts using an interface. ICS provides a single public IP address to connect to the Internet, fixed address range for hosts, DNS proxy for name resolution, and automatic IP addressing. ICS is also easy to configure. You can use ICS to connect the whole network to the Internet. Private IP addresses are hidden from the public network. Public external addresses are used over the public network. ICS includes the Internet Connection Firewall service for securing the internal private network. One of the main features of using ICS is that it is preconfigured. ICS automatically configures the internal address of the computer hosting the shared connection as 192.168.0.1. Internal clients are assigned addresses in the 192.168.0.0/24 address range. Internal clients exist on the identical physical subnet. All internal clients point to the ICS computer for DNS resolution. The shared external interface has a single public address. You can install ICS using Network And Dial-Up Connections.
ICS is supported by:
-
Windows 98 Second Edition
-
Windows Me
-
Windows XP
-
Windows 2000 Professional
Using Virtual Private Networks (VPNs) for Internet Connectivity
Virtual private networks (VPNs) enable users to connect to a remote private network through the Internet. With a VPN, data is first encrypted and encapsulated before it is sent to the remote VPN server. When the VPN server obtains the data, it decrypts the packet so that is can be interpreted. VPNs are usually implemented to provide connectivity between two or multiple private networks or LANs, and to enable remote access users to connect to and access the network. Many companies supply their own VPN connections via the Internet. Through their ISPs, remote users running VPN client software are assured private access in a publicly shared environment. By using analog, ISDN, DSL, cable technology, dial and mobile IP; VPNs are implemented over extensive shared infrastructures. Email, and database and office applications use these secure remote VPN connections.
A VPN gateway, also called a VPN router, is a connection point that connects two LANs which are connected by a nonsecure network such as the Internet. A VPN gateway connects to either a single VPN gateway, or to multiple VPN gateways to extend the LAN.
Tunneling is the terminology used to describe a method of using an internetwork infrastructure to transfer a payload. Tunneling is also known as the encapsulation and transmission of VPN data, or packets. The tunnel is the logical path or connection that encapsulated packets travel through the transit internetwork. The tunneling protocol encrypts the original frame so that its content cannot be interpreted. The encapsulation of VPN data traffic is known as tunneling.
With Internet-based VPNs, the remote client connects to the Internet and then utilizes VPN client software to establish a connection with the VPN server. All communications between the client and VPN server are encrypted and encapsulated into packets before being transmitted over the public Internet.
Windows Server 2003 has a VPN component included with Routing and Remote Access service (RRAS) of Windows Server 2003 that enables you to configure a Windows Server 2003 computer as a VPN server. You can use the VPN server t enable clients to remotely access the network. Because remote clients typically already have Internet connectivity, you can set up the VPN server to allow the Internet connections from these clients.
In addition to configuring an Internet-based VPN, you can also configure router-to-router VPNs if you want to connect two physically separated LANs. Router-to-router VPNs are also typically called demand-dial connections. This is due to the connection only being established when traffic needs to pass between the LANs. For a router-to-router VPN configuration to work, a internet connection is needed for each separated LAN. Traffic is then encapsulated on the Internet to create the virtual connection between the two LAN locations.
Using demand-dial connections for small remote sites that only require intermittent VPN connectivity is ideal. Here, you can configure a demand-dial VPN with one-way initiation or with two-way initiation:
-
One-way initiation; the client of one VPN server initiates the connection and the other VPN server is configured to accept the connection.
-
Two-way initiation; clients of both VPN servers can initiate the connection and each VPN server is configured to accept the connection.
An alternative to using demand-dial connections is the utilization of a persistent connection to the Internet. Dedicated leased lines are classed as being persistent connections. This means that the connections are permanent connections, and remain open all the time. A VPN server set up to use persistent Internet connections can make the connection available to VPN clients.
A VPN tunneling protocol is required to create a VPN. The VPN tunneling protocol provides the tunnel which will be used to send private data as encrypted data over the Internet. The VPN tunneling protocols used to encapsulate data and manage VPN tunnels are:
-
Point-to-Point Tunneling Protocol (PPTP): PPTP, an extension of Point-to-Point Protocol (PPP), encapsulates PPP frames into IP datagrams to transmit data over an IP internetwork. Windows Server 2003 includes PPTP version 2. To create and manage the tunnel, PPTP utilizes a TCP connection. A modified version of Generic Route Encapsulation (GRE) deals with data transfer by encapsulating PPP frames for tunneled data. The encapsulated tunnel data can be encrypted and/or compressed. However, PPTP encryption can only be utilized when the authentication protocol is EAP-TLS or MS-CHAP. This is due to PPTP using MPPE to encrypt VPN data in a PPTP VPN, and MPPE needing EAP-TLS or MS-CHAP generated encryption keys. With the Windows Server 2003 implementation of PPTP, both 40-bit encryption and 128-bit encryption is supported.
-
Layer Two Transport Protocol (L2TP): L2TP encapsulates PPP frames, and sends encapsulated data over IP, frame relay, ATM and X.25 networks. With L2TP, the PPP and layer two end-points can exist on different devices. L2TP can also operate as a tunneling protocol over the Internet. L2TP uses UDP packets and a number of L2TP messages for tunnel maintenance. UDP is used to send L2TP encapsulated PPP frames as tunneled data. When L2TP is used with IPSec, the highest level of security is assured. This includes data confidentiality and integrity, data authentication, as well as replay protection. IPSec protects the packets of data and therefore provides security on nonsecure networks such as the Internet.
Remote access policies can be used to secure demand-dial connections. You can use a remote access policy to control whether or not a user is allowed to connect to VPN server. Remote access policies contain conditions which you specify through the Routing and Remote Access management console. These conditions determine which users are allowed to connect to the remote access server. Remote access policies can also be used to specify which authentication protocol clients must utilize; specify which encryption methods clients must utilize; and to restrict user access based on user and group membeship, and time of day.
Identifying Internet Connectivity Requirements
In order to implement an effective Internet connection strategy, there are a few factors that you need to consider and a few Internet connectivity requirements which you need to determine, including the following:
-
When defining any Internet connection design or strategy, one of the foremost factors which need to be determined, is the amount or quantity of bandwidth needed for users to perform their necessary tasks. To determine the bandwidth needed by users, you have to determine the following:
-
The number of users which will most likely be accessing the Internet concurrently.
-
The applications which will be used by these users
-
The tasks or functions which users will perform.
The amount of bandwidth required affects the following:
-
Which ISP you need to utilize.
-
What costs need to be met
-
-
Determining when the organization's peak Internet bandwidth usage times are, is another issue that needs to be determined. For instance, organizations that operate 24 hours a day would require more bandwidth than another organization running between 8am and 5pm. In addition, you have to remember to provide for non-Internet connection operations, such as off-site backups, that could require a large quantity of bandwidth as well.
-
Another important requirement that needs to be determined when you define your Internet connectivity strategy is to determine the number of users which will need Internet connections. This can be broken into a number of factors:
-
How many employees within the company who use computers connected to the private network need connections to the Internet.
-
How many of the Internet connections required would be concurrent connections.
-
How long will users need to be connected to the Internet.
-
-
Determining the locations of computers that need Internet connectivity is also important. The location of computers have an impact on the following:
-
Where routers and other Internet connection devices should be placed.
-
Whether the router should be connected to the backbone network.
-
Whether Internet connection devices should be located within a single area.
-
-
The next important factor pertains to the applications that users will run. Factors to include under this requirement are listed here:
-
The manner in which users will use Internet applications.
-
Determine the functions users will perform using Internet applications, and then attach bandwidth requirements to each of these functions.
-
Determining Bandwidth Requirements for Internet Connections
One of the key requirements for Internet connections is the availability of sufficient bandwidth for traffic using the Internet connections. Having sufficient hardware equipment and connections to the Internet means nothing if you have insufficient bandwidth.
When determining the bandwidth requirements for Internet connectivity, you have to remember to include the bandwidth requirements of your other services that use the organization's bandwidth.
The main elements that affect bandwidth for Internet connections are listed here:
-
The type of e-mail sent. Different e-mail types have different bandwidth requirements.
-
The type of traffic passing over the Internet connections. Remember too that an Ethernet 10 Mbps link usually only means that 10 Mbps of data will be able to be sent. This is because of factors such as collision and noise.
Resolving the issues listed here should be included in the overall bandwidth requirement calculation for your Internet connections:
-
Whether Dynamic Host Configuration Protocol (DHCP) associated traffic, or DNS associated traffic will be using the link. If yes, then it is reommended that you run both the DHCP service and the DNS service on the same server.
-
Whether e-mail traffic will be using the link. E-mail is the common cause of available bandwidth being depleted.
-
Whether Voice over IP (VoIP) will be utilizing the connection. VoIP creates additional traffic that in turn has bandwidth requirements.
-
Whether operations such as Web browsing will be allowed with the Internet connections.
Database applications that transfer a large quantity of data, and some graphical-based applications also need sufficient bandwidth resources. Any additional services that could possibly be using the link should be provided for in terms of bandwidth.
Defining Redundancy for your Internet Connectivity Strategy
If the nature of the business of the company heavily relies on the Internet to perform its key business activities, then having a single method of accessing or connecting to the Internet could be an issue that needs to be resolved when you design your Internet connectivity strategy. Here, it should be compulsory to have at least two methods of connecting to the Internet.
Before implementing redundancy for your Internet connectivity design, you should first determine whether redundancy is actually required, and if yes, the next step would be to determine the level of redundancy required.
The issues which you need to clarify on redundancy for your Internet connectivity solution are summarized here:
-
Determine whether redundancy is required. The nature of the business of the company would determine whether redundancy is needed or not.
-
Determine the time duration for which the company can operate without Internet connections being available.
-
Determine the cost factor associated with a loss of Internet connectivity.
-
Determine which internal services are dependent on the availability of Internet connectivity. A loss of Internet connectivity would mean that remote users would not be able to access internal resources over a VPN connection. You should attempt to determine the cost associated with mobile users and remote users not being able to access the company network.
-
Determine whether the company can lose customers because of a loss of Internet connectivity.
-
Determine whether there are any existing Internet connections that do provide some level of redundancy.
Determining the Internet Connection Type
The different WAN technologies which can be used for Internet connections are listed below:
-
Dial-up modem: Dial-up modem connections are ideal if your organization only consists of a small number of users that do not need to connect to the Internet on a regular basis. This is due to dialup modem connection only being able to meet the bandwidth requirements of a small number of users. Modems can be installed on a computer, and then shared through the Windows Internet Connection Sharing (ICS) service.
A few characteristics of dial-up modem connections are:
-
A dial-up modem connection can only reach up to 53 Kbps.
-
Provide e-mail for a maximum of 10 concurrent users.
-
Provide large FTP downloads for only 1 to 2 simultaneous users.
-
Provide Web browsing for 2 to 3 concurrent users.
-
-
Integrated Services Digital Network (ISDN): ISDN is a digital dial-up service that utilizes telephone cabling and other technology to provide Internet connections. The different types of ISDN services are ISDN Basic Rate Interface (BRI) and ISDN Primary Rate Interface (PRI).
The main characteristics of ISDN Basic Rate Interface (BRI) are listed here:
-
BRI connections work well for small companies
-
BRI connections are available from quite a number of telephone companies.
-
ISDN BRI can offer 128 Kbps of bandwidth.
-
Provide e-mail for a maximum of 20 concurrent users.
-
Provide large FTP downloads for only 3 to 4 simultaneous users.
-
Prvide Web browsing for 6 to 8 concurrent users.
The main characteristics of ISDN Primary Rate Interface (PRI) are listed here:
-
ISDN PRI can offer 1.544 Mbps transmission speed.
-
Provide e-mail for a maximum of 120 concurrent users.
-
Provide large FTP downloads for only 40 to 50 simultaneous users.
-
Provide Web browsing for 75 to 100 concurrent users.
-
-
Cable television networks (CATV): While CATV networks are used mainly for the home environment; it can be used as a technology to provide Internet connections for an organization. The actual bandwidth provided by CATV networks is determined by the number of subscribers within the local area. Available bandwidth is reduced when other subscribers within the same local area transmit large quantities of data.
The main characteristics of CATV networks are listed here:
-
Transmission speed: Maximum of 512 Kbps downstream, and a maximum of 128 Kbps upstream.
-
Provide e-mail for about 50 concurrent users
-
Provide large FTP downloads for 12 to 15 simultaneous users.
-
Provide Web browsing for 25 to 30 concurrent users.
-
-
Digital Subscriber Line (DSL): A DSL link is a dedicated connection between two sites which is provided as a service from a telephone company. Bandwidth is predefined for a DSL connection. While there are a few different types of DSL connections, the most commonly used DSL connections for Internet connections is Asymmetrical Digital Subscriber Line (ADSL). An asymmetrical connection uses different speeds in each direction.
The main characteristics of ADSL are listed here:
-
Transmission speed: Maximum of 640 Kbps downstream, and a maximum of 160 Kbps upstream.
-
Provide e-mail for about 60 concurrent users
-
Provide large FTP downloads for 15 to 18 simultaneous users.
-
Provide Web browsing for 30 to 35 concurrent users.
-
-
Leased/dedicated lines: These are permanent connections between two sites that have a predetermined quantity of bandwidth. There are also different types of leased lines. The leased lines typically used to connect networks to the Internet are T-1 connections. Another type of leased line, a T-3 connection, is used to for backbones and by ISPs.
The main characteristics of T-1 connections are listed here:
-
Transmission speed: Maximum of 1.544 Mbps
-
Provide e-mail for about 120 concurrent users
-
Provide large FTP downloads for 40 to 50 simultaneous users.
-
Provide Web browsing for 75 to 100 concurrent users.
The main characteristics of T-3 connections are listed here:
-
Transmission speed: Maximum of 44.736 Mbps
-
Provide e-mail for about 3, 000 concurrent users
-
Provide large FTP downloads for 1, 000 to 1, 500 simultaneous users.
-
Provide Web browsing for 2, 000 to 3, 000 concurrent users.
-
-
Frame Relay: With frame relay, a variable quantity of bandwidth is available, and the cost of bandwidth is determined by the actual bandwidth utilized. With frame relay, the cloud which is the frame relay network is maintained by a service provider. The quantity of bandwidth needed is negotiated with the service provider. With frame relay, bandwidth is called the committed information rate (CIR). The CIR is available and always guaranteed. If the CIR is surpassed, an additional fee is incurred, and if usage falls beneath the CIR, then the bandwidth fee is based on the bandwidth utilized.
Determining the Router Type for Internet Connectivity
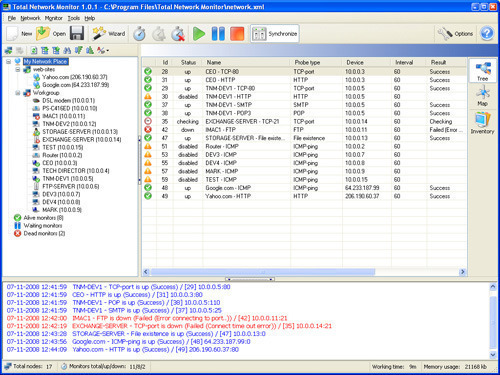
You can use the Windows Server 2003 Routing and Remote Access Service (RRAS) feature to route traffic between the LAN and public network. As mentioned previously, RRAS includes the full NAT implementation which can be used to translate private IP addresses to a public IP address that can be routed over the Internet.
For the private network, a router must be installed. The ISP provides th router connected at the other end of the WAN link. You can use stand-alone Internet hardware routing devices to connect the LAN to the WAN and provide Internet connections. By connecting stand-alone Internet routers directly to the WAN, you can share dial-up modem, ISDN or DSL connections with the network. Hardware routers are dedicated routing devices thats sole purpose is to provide a routing capability. Hardware routers are ideal for providing Internet connections for the organization. Software routers run as a service on a computer residing within the network.
The router which you install will operate as the default gateway of the network for all IP addresses which are not located within the private network.
Evaluating Different ISPs (Internet Service Providers)
The ISP which you decide to utilize for your Internet connectivity strategy has quite a significant influence on the effectiveness of your Internet connectivity design and implementation. A few factors which you should consider and ponder over when assessing the different ISPs, and the features offered by each ISP are listed here:
-
Whether the ISP provides security features such as firewall features or intrusion detection mechanisms.
-
Whether the ISP provides the following:
-
VPNs using Point-to-Point Tunneling Protocol (PPTP) OR
-
Layer 2 Tunneling Protocol (L2TP) with Internet protocol security (IPSec)
-
-
The manner in which the ISP is connected to peers.
-
Whether multiple vendors are used for the establishing the complete Internet connection. In some cases, one vendor is responsible for the physical connection or link, and the ISP is only responsible for connecting to the Internet.
-
Whether the ISP provides service-level agreements.
-
What the different WAN connection types offered by each ISP are. These can be classified as follows:
-
Leased lines:
-
Digital Subscriber Line (DSL)
-
T-carrier lines
-
E-carrier lines
-
-
Circuit switched connections:
-
Modems
-
Integrated Services Digital Network (ISDN)
-
-
Packet switched connections:
-
Frame relay
-
X.25
-
Virtual Private Networks (VPNs)
-
Asynchronous Transfer Mode (ATM)
-
-
-
The manner in which Internet usage is monitored by the ISP.
The primary function which the ISP has to provide for your Internet connectivity design is to provide access to the Internet.
ISPs also provide a number of other services, including the following:
-
Some ISPs can support different WAN connection types, and can also offer a range of different levels of bandwidth.
-
Most ISPs provide at least one registered address to connect your router or proxy server to the Internet. Depending on the extent of your Internet connectivity strategy, you might need to obtain additional registered IP addresses.
-
The e-mail services provided by ISPs are usually insufficient for medium sized and large sized organizations that need a large number of e-mail accounts. In these cases, an organization can implement and manage its own mail servers. For a mail server to support Internet e-mail, the following is required:
-
A registered IP address which Internet mail servers can forward e-mail to.
-
Domain registered in DNS.
-
-
In most cases, organizations use their own DNS servers for name resolution services, and not the DNS servers of the ISP. Windows Server 2003 includes a DNS server which you can use to provide name resolution services to Internet clients.
-
ISPs can be used to host the organizations Web sites, or an organization can run and manage their own Web sites. The requirements for running Internet Web servers are listed here:
-
For Internet users to access the Web servers, the addresses of these Web servers have to be registered in DNS.
-
You also need to implement security mechanisms, such as firewalls, to scure the Web servers.
-
Determining Internet Connectivity Security Requirements
Determining the security requirements for your Internet connectivity solution should include the following:
-
The security requirements dictated by the organization and the nature of its business.
-
The level of Internet access which will be granted to users.
-
The manner in which to implement Internet security requirements.
A few measures that you can implement to prevent internal users from accessing the Internet, or limit users from performing certain activities include:
-
Limit the bandwidth which users can utilize.
-
Specify a time period for which users can access the Internet.
-
Specify the sites which users can access.
An organization usually consists of different types of users needing different levels of Internet access to perform their functions. The methods which can be used to assign different levels of access to different users are:
-
Through packet filtering, you can define the ports that every computer residing on the private network is allowed to use. Packets can be filtered on:
-
IP address
-
Port numbers
-
-
You can use proxy server mechanisms, such as a internet Security and Acceleration (ISA) server to limit user access to the Internet and to limit access to only certain Internet services.
You can also control which Internet applications users are able to access and run. One method of limiting the Internet applications that users can execute is by filtering packets based on port numbers. TCP/IP packets include a source port number that indicates the application which created it; and a destination port number that indicates the application receiving the packet. Here, you can use a firewall to provide the packet filtering solution. If you configured a computer through Routing and Remote Access management console as your router, then you can configure the router to filter packets.

Ganesh Avasthi
very nice article but i want to ask more.
1) by how many ways two branches employee access each others resources ??
sudha
I have need details about leasing the bandwidth. Our organisation have planned to provide internet services to 3000 people and i want to know much much bandwidth should i lease it and how should i calculate the bandwidth requirement