Cell phone cloning refers to the act of copying the identity of one mobile telephone to another.
This is usually done to make fraudulent telephone calls. The bill for the calls go to the legitimate subscriber. This made cloning very popular in areas with large immigrant populations, where the cost to “call home” was very steep. The cloner is also able to make effectively anonymous calls, which attracts another group of interested law breakers.
Cell phone cloning started with Motorola “bag” phones and reached its peak in the mid 90’s with a commonly available modification for Motorola “brick” phones such as the Classic, the Ultra Classic, and the Model 8000.
Cloning involved modifying or replacing the EPROM in the phone with a new chip, which would allow one to configure an ESN (Electronic Serial Number) via software. The MIN (Mobile Identification Number) would also have to be changed.

After successfully changing the ESN/MIN pair, the phone would become an effective clone of the other phone.
Cloning required access to ESN and MIN pairs. ESN/MIN pairs were discovered in several ways:
- Sniffing the cellular network
- Trashing cellular companies or cellular resellers
- Hacking cellular companies or cellular resellers
Cloning still works under the AMPS/NAMPS system, but has fallen in popularity as older phones that can be cloned are more difficult to find and newer phones have not been successfully reverse engineered.
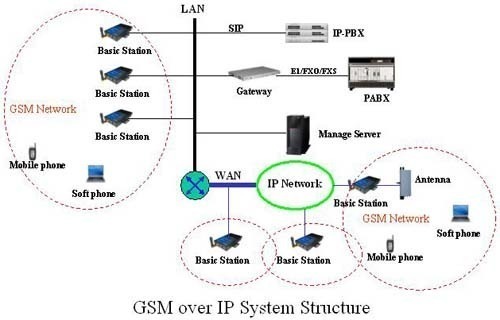
Cloning has been successfully demonstrated under GSM, but the process is not easy and currently remains in the realm of serious hobbyists and researchers. Furthermore, cloning as a means of escaping the law is difficult because of the additional feature of a radio fingerprint that is present in every mobile phone’s transmission signal. This fingerprint remains the same even if the ESN or MIN are changed. Mobile phone companies can use the mismatch in the fingerprints and the ESN and MIN to identify fraud cases.


SquinklaPsyOps
Laredo Texas has a big history of cloning phones.
suchitra
well i ve my seminar i need proper ppt regarding this mobile phone clonig.
bill
can a cloned phone call itself?? well -the other phone or only leave voicemail? sounds like an excellent idea -if its legal- to do for yourself, then i can stop having to run out to the barn to get my phone out of the truck in the middle of the nite, keep one in the house for emergencies when i am not home
Hemangi
I have gv this topic mobile phone cloning for seminar,
but,i want more informations like advantages,diadvantages,
aaplications.
Kaitlyn
So I have an iPhone4 and I have been receiving calls and text messages from my friends when they are in the same room as me. But when I look at their call log list, my contact is not there. If you are familiar with iPhones you cannot delete one call without deleting the entire call log. Then, if I tell them they texted me and read the message and they go to their phone, they don’t remember it and it’s not on there and my last message will be from 2-3 days ago. Was my phone cloned or would it be theirs…?
ej
Is there a way to find out if one’s phone has been cloned? And if it has been cloned, how can one get it “un-cloned”?
pushpa
as i have gv a seminar on mobile phone cloning plz provide me the applications,advantages ,disadvantages and future enhancement to mobile phone cloning
ashutosh
good.. sir g , i want to have a ppt regarding cell phone cloning
Thomas Hansen
Maybe your cellphone was hacked … Do you have bluetooth enabled ?
MTGirl77
What does this sound like? Last month, I travelled with my kids and stayed at an airport hotel during a layover. We went to bed as soon as we got in (11pm). I never look at my cell bill but needed to find a number. I was shocked to see 3 short calls on the night we stayed at the airport between 2-3 am. They all originated from where I was. I called the #’s and one answered- it was a girl who told me she was an “erotic provider”. I did a search of the #’s and they were all found in multiple ads for escorts on craigslist. Yah right! I guarantee I didn’t make those calls and if my kids (2 & 4) happened to wake up in the middle of the night, I doubt they’d randomly dial 3 hookers. I called Verizon and was told that my BB Storm was impossible to clone. The rep said he had no idea. I’m not crazy, I know I didn’t call those numbers. But it is hard to believe that someone would go to the trouble to clone my phone just to make a couple free calls in the middle of the night. Any ideas?