Breaking into secured networks or computers is not an easy job, especially with the level of security some companies employ. Still, the fact remains – anything the mind of man can conjure can be broken into – and this is a challenge that no hacker can resist.
Understanding the means by which hackers pursue their nefarious activities is one way of dealing with the problem; knowing how they do it provides you with a basis for developing countermeasures. Among the tools that hackers use are:
Password-Cracking Tools
People and organizations that rely solely on passwords for security are at greater risk than those who use multi-factor authentication systems. This is because new computers can process more information in less time than ever before; password-cracking tools such as automated dictionary attacks have become more powerful and process faster with the latest computer processors.
Manufacturer’s Defaults
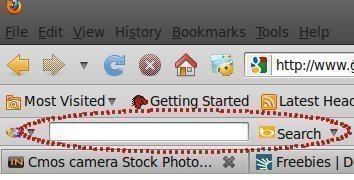
Turn on your Internet browser and do a search for “default passwords” – you’ll find numerous sites that can provide you with detailed information on default settings – including access codes, settings, and passwords that are used by hardware and software manufacturers when programming their products prior to delivery.
Hackers make use of these for planning attacks on networks and standalone computers. The best defense against these is to do the unexpected – change and remove the manufacturer’s default settings before even uploading new products or installing additional software.
Data Mining
Many hackers spend a lot of time preparing for their attacks – including conducting in-depth research into the targeted companies, key officers and authority figures, and so on using readily available information in the public domain.
Infiltration and Espionage
Most security measures are directed against external threats; what security experts do not want to talk about is the fact that internal threats form a far more insidious approach for hackers.
While some hackers may make the effort of joining a company in order to get data from within, there are other ways of getting inside information. Disgruntled employees, bribes, lax measures such as allowing passwords of terminated employees to remain (such passwords can be sold) are some of the ways that hackers can get information.
Con Games
Confidence’ games aimed at generating inside information that can be used in an attack are part and parcel of a hacker’s tool kit. The objective of the exercise is to gain the confidence of key people in the organization, and use information as a starting point to infiltrate company networks or personal computers.
There are documented cases of hackers posing as IT services people calling up employees by phone and ‘demanding’ privileged information such as passwords and account numbers. Most people, when confronted with such a move, usually give in – unwittingly providing hackers with a means of breaking into the network.
Trojan Horses
A Trojan horse is malicious code carried as a ‘payload’ of an application (malicious or benign). A Trojan horse can open a backdoor into a system or network through which an unscrupulous individual can gain access to confidential information.


Follow Us!