A wireless network key is an encryption key for that prevents unauthorized users from accessing a specific wireless network. The user creates wireless network keys, which either a wireless router or a computer that is connected to that wireless router can manage. Wireless network keys can be any length greater than eight characters and can be used with both WEP and WPA encryption methods.
A wireless network key serves as a password for a specific wireless network and prevents unauthorized users from accessing it. Wireless network keys can be used with both WEP and WPA, but WPA provides the maximum level of security. WEP (Wired Equivalent Privacy) has been used since 1999 and was originally designed to provide users with the same level of security that they would find in a LAN (Local Area Network). However, WEP is outdated and leaves the user vulnerable to attack. WPA (WiFi Protected Access) removes this vulnerability by providing the user with better key management, integrity checking, and more possible key combinations.
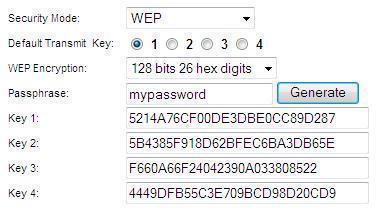
WEP Key Passphrase
WEP stands for “Wired Equivalent Privacy”, and is a part of IEEE 802.wireless network standard. It was introduced to provide security to wireless networks in view of their vulnerability to eavesdropping because of their use of radio waves. WEP uses the stream cipher RC4 for confidentiality. A WEP key is therefore a security code that is generated with this protocol. WEP keys allow computers on a network to exchange encoded messages with one another while hiding the messages’ contents from intruders. This key is what is used to connect to a wireless-security-enabled network.
A WEP key passphrase is a sequence of words or ordinary text that can be used to automatically generate a WEP key. They are generally longer and stronger than most passwords and can go from 8 to 63 ASCII characters. Uppercase, lowercase, and even numeric characters can be used to form a passphrase. However, this may weaken the key and make it vulnerable to a dictionary attack. To protect from this kind of brute force attack, use Wi-Fi Protected Access (WPA) to automatically generate unique keys. WPA generates unique keys by employing the Temporal Key Integrity Protocol (TKIP) along with the network service Set Identifier (SSID) to generate unique keys for each wireless client.
A WEP key consists of a string of hexadecimal characters, which include the numbers 0-9 and the letters A-F. Each character represents 4 bits of the key.
The length of a WEP key depends on the type of WEP encryption used. The various WEP key lengths are as follows:
- 64-bit WEP uses a 40-bit key
- 128-bit WEP uses a 104-bit key.
- 152-bit WEP key.
- Preshared 256-bit WEP key
The strength of the protection that the encryption gives depends on the encryption key choice.
Some security limitations of WEP include the following:
- The key size, as cracking a longer key will require more packets to be intercepted.
- The possibility of IV collisions and altered packets, which a longer key does not help at all.
- WEP uses RC4 to protect the confidentiality of the transmitted data. Because every device on the network uses one key to encrypt every transmitted packet, an eavesdropper could intercept the WEP encryption and find the key.
WPA is more secure and easier to use than WEP. It requires configuring a router with a passphrase that WPA will use to generate a WEP key.
An alternative is to use WEP key generators. There are several such tools available on the Internet. A WEP key generator generates random hexadecimal values from a passphrase value entered.
Either use a WEP key or a passphrase to connect a router to the network. Most routers provide for this. If the router is set to WEP, enter the WEP key. If the router is set to WPA, set the passphrase to be used to connect to the network.



james cochrane
I am having trouble setting up a net gear wi fi extender. It asks me for the existing passkey for the linksys wireless G router that I have. I can’t find the passkey. How can I reset it and start over again?
Ajay Khule
Hi James!
Resetting the router to the factory defaults will delete any changes you have made to the router, including any security settings. This should be used as a last resort.
You can visit to respective link for more details.
Thanks!
ahamad
how can use wifi the problum is sey invalid network key
Bob Loblah
The second bullet point should be
128-bit WEP uses a 104-bit key.