WPA (Wi-Fi Protected Access) is an interim standard by the WiFi Alliance to comply with the security protocol designed for wireless security. WPA will most likely be rolled into an eventual IEEE 802.11i standard. This protocol was an outcome of numerous severe flaws researchers had discovered in the preceding wireless security system called Wired Equivalent Privacy (WEP).
WPA (W-Fi Protected Access) Modes of Operations
WPA (Wi-Fi Protected Access) features two very different modes of operation:
| WPA Enterprise Mode | WPA PSK (Pre-Shared Key) Mode |
|---|---|
| Requires an authentication server | Does not require an authentication server |
| Uses RADIUS protocols for authentication and key distribution | Shared secret is used for authentication |
| Centralizes management of user credentials | Device-oriented management of user credentials |
The PSK (Pre-Shared Key) Mode of WPA is vulnerable to the same risks as any other shared password system, such as dictionary attacks. PSK Mode also suffers from the same key management difficulties as any system where the key is shared among multiple users, such as the difficulties in removing a user once access has been granted.
The Enterprise Mode of WPA benefits from the maturity of the RADIUS architecture — but it requires a RADIUS server. This is not something that will benefit most home users.
Security Enhancements in WPA (Wi-Fi Protected Access)
WPA provides additional security by:
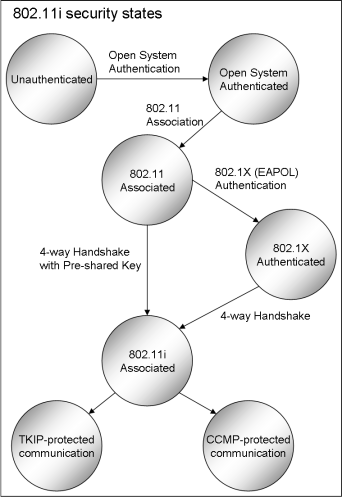
- Requiring authentication using 802.1X
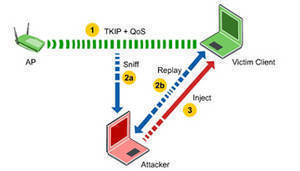
- Requiring re-keying using TKIP
- Augmenting the ICV (Integrity Check Value) with a MIC (Message Integrity Check), to protect the header as well as the payload
- Implementing a frame counter to discourage replay attacks
WPA2
In addition to WPA, some vendors also implement WPA2, which allows the use of AES instead of RC4. WPA2 necessitates certification and testing by the Wi-Fi Alliance. WPA2 makes use of the compulsory elements of 802.11i. It principally establishes a fresh AES-based algorithm, CCMP, which is believed to be totally secure.

susan_weber7