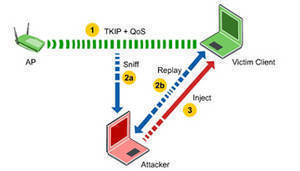
TKIP (Temporal Key Integrity Protocol) is part of a draft standard from the IEEE 802.11i working group.
TKIP utilizes the RC4 stream cipher with 128-bit keys for encryption and 64-bit keys for authentication.
TKIP is an enhancement to WEP (Wired Equivalent Privacy) security.
TKIP enhances WEP by adding a per-packet key mixing function to de-correlate the public initialization vectors (IVs) from weak keys.
TKIP also enhances WEP by adding a rekeying mechanism to provide fresh encryption and integrity keys. This makes TKIP protected networks more resistant to cryptanalytic attacks involving key reuse.
Before TKIP, it was possible to perform a known ciphertext attack on WEP after collecting a large number of packets.
TKIP significantly mitigates the WEP key derivation vulnerability but does not provide complete resolution for the weaknesses.
TKIP is Being Replaced by RSN
The RSN (Robust Secure Network) component of the 802.11i standard recommends replacing TKIP with CCMP. However, the standard does allow TKIP for backwards compatibility.
This backwards compatibility with TKIP is necessary because most legacy Wi-Fi (802.11) hardware does not have the CPU power to use the AES algorithm utilized by CCMP. The RC4 algorithm utilized by TKIP will run on legacy Wi-Fi hardware.
Additional Reading on TKIP
For more information on TKIP, read 802.11 Security Series Part II: The Temporal Key Integrity Protocol (TKIP).
Some analysts use the name TKIP to refer to the functionality of both TKIP and MIC (Message Integrity Check).



Sue
Hi!
My printer status has become “offline”. When I try to re-configure the printer it asks me for the TKIP number. Does anyone know what this is and where I might find it?
Sue
memenode
You might find it in your router’s wireless settings.